Documentation Index
Fetch the complete documentation index at: https://tyk.io/docs/llms.txt
Use this file to discover all available pages before exploring further.
Introduction
Single sign-on (SSO) enables users to access multiple applications using one set of login credentials, reducing the burden of password management and improving security. SSO is relevant for businesses of all sizes, streamlining access control and improving user experience. Regardless of your organization’s size, implementing SSO can enhance security, simplify access to enterprise resources, and strengthen user satisfaction. In this section, you’ll learn how to enable single sign-on for admin users and developers in the Tyk Enterprise Developer portal with 3rd party identity providers (IDPs). Prerequisites- A Tyk Enterprise portal installation
- Supported 3rd party identity provider up and running
Portal SSO Configuration Options
Tyk Enterprise Developer Portal uses the Tyk Identity Broker (TIB) to integrate Tyk authentication with 3rd party identity providers (IDPs). From portal version 1.12.0, TIB is embedded in the portal. With this, you have two options to configure SSO in the portal:- Using Embedded TIB: No need to install it separately.
- Using External TIB: If you are using a previous version of the portal, you can still use SSO with TIB installed as a separate application.
Configuring SSO with Embedded TIB
Configuring SSO with Embedded TIB is a four-step process:Enabling Embedded TIB
To enable Embedded TIB in the portal, add thePORTAL_TIB_ENABLED variable to the portal .env file:
The Tyk Enterprise Developer Portal embedded TIB only supports OIDC, LDAP or Social SSO providers.
Understanding UserGroup Mapping
The Tyk Enterprise Developer portal has two audiences:- Developers: Developers created by the sso flow are portal users that belong to an organization and team/s, if a user group mapping is not specified, they are assigned to the default organization and default team. Developers created by the sso flow are always assinged the Consumer Super Admin role. If part of an organization and a team, this means that the developer is a super admin for that organization. Read more about managing api consumer organizations here.
- Admins: Admins created by the SSO flow are portal users who do not belong to any organization (OrgID is 0) and are assigned the Provider Admin role.
Default behaviour of UserGroup Mapping
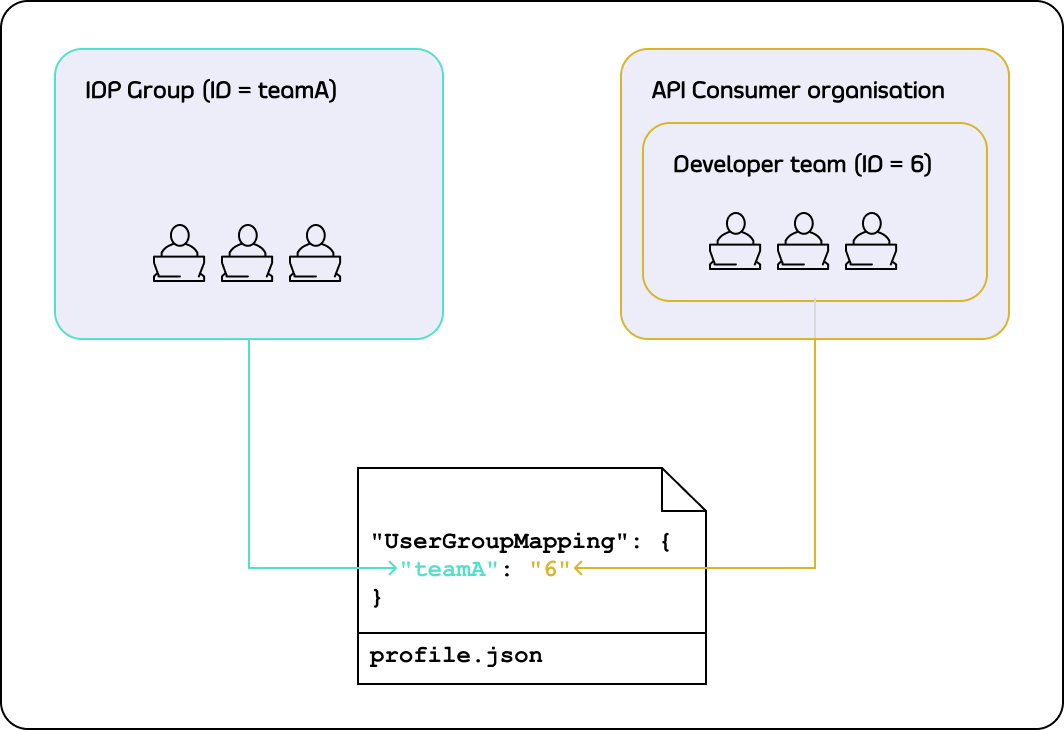
TheUserGroupMapping object contains keys that refer to group IDs in your IDP, and the corresponding values are team IDs in the portal.
When the Tyk Identity Broker authorizes a user, it searches for a key that matches the user’s group ID in the IDP.
If TIB can’t find a matching group ID, it logs the user in to the team with an ID equal to DefaultUserGroupID in the portal (if DefaultUserGroupID is defined).
We recommend always defining DefaultUserGroupID and ensuring it refers to a valid team ID in your portal instance. The portal will refuse login attempts if DefaultUserGroupID is defined but refers to an invalid team ID.
If no matching group ID is found in the UserGroupMapping object and DefaultUserGroupID isn’t defined, the portal logs in the user to the “Default organization | All users” team with an ID of 1.
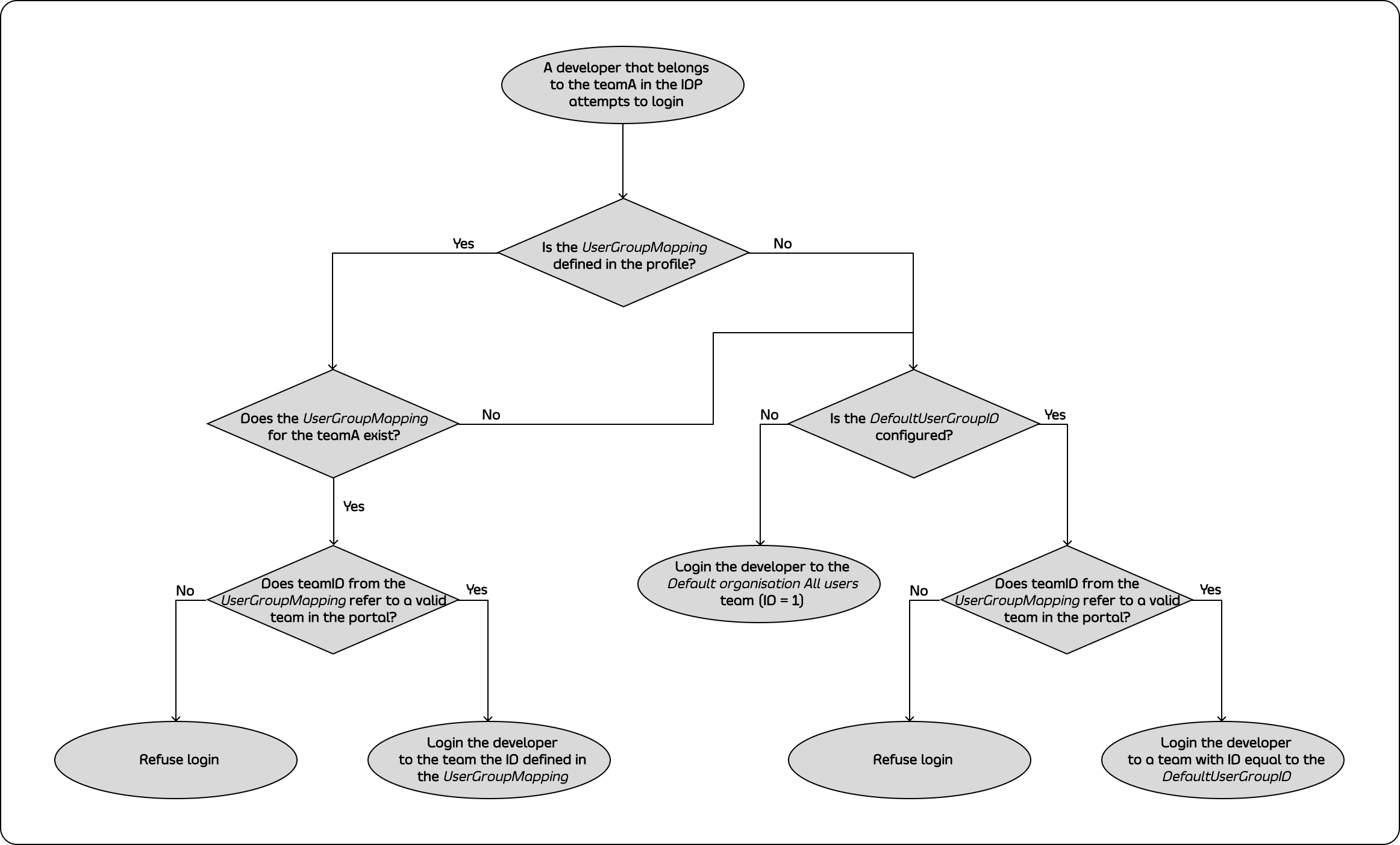
Login Evaluation Algorithm
To determine whether a developer should be allowed to log in and which team they should be logged into, the portal uses the following algorithm: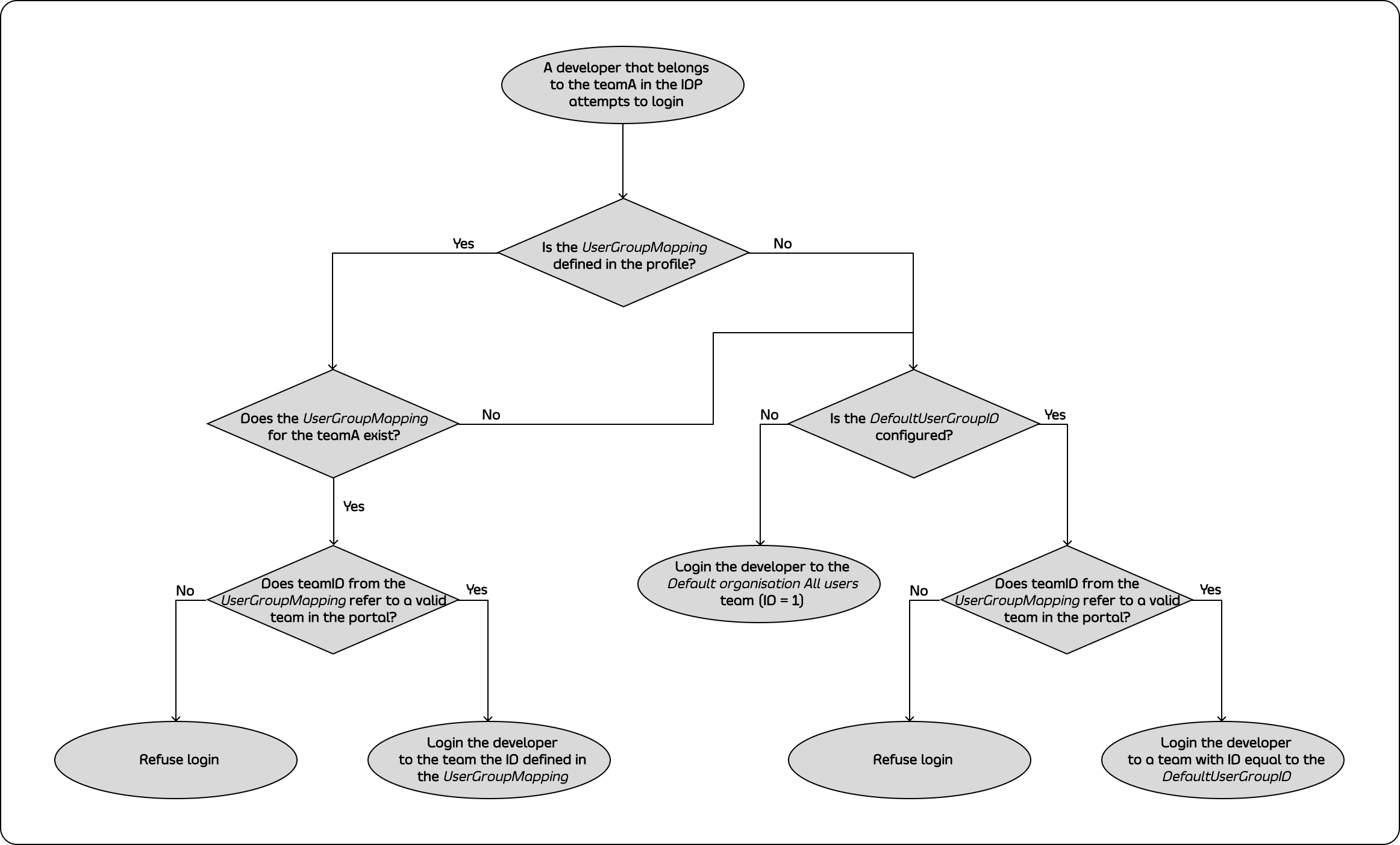
Creating TIB Profile
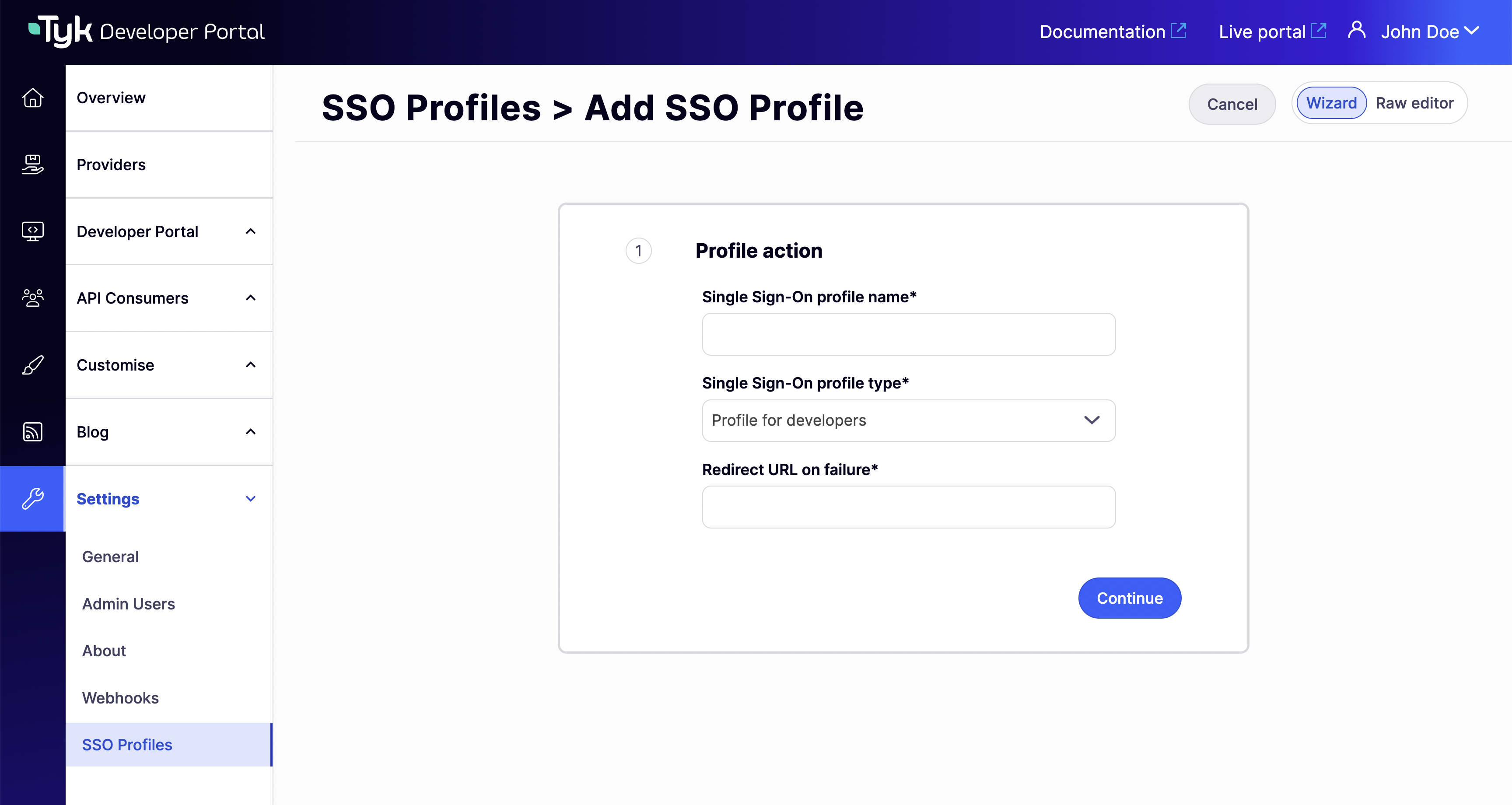
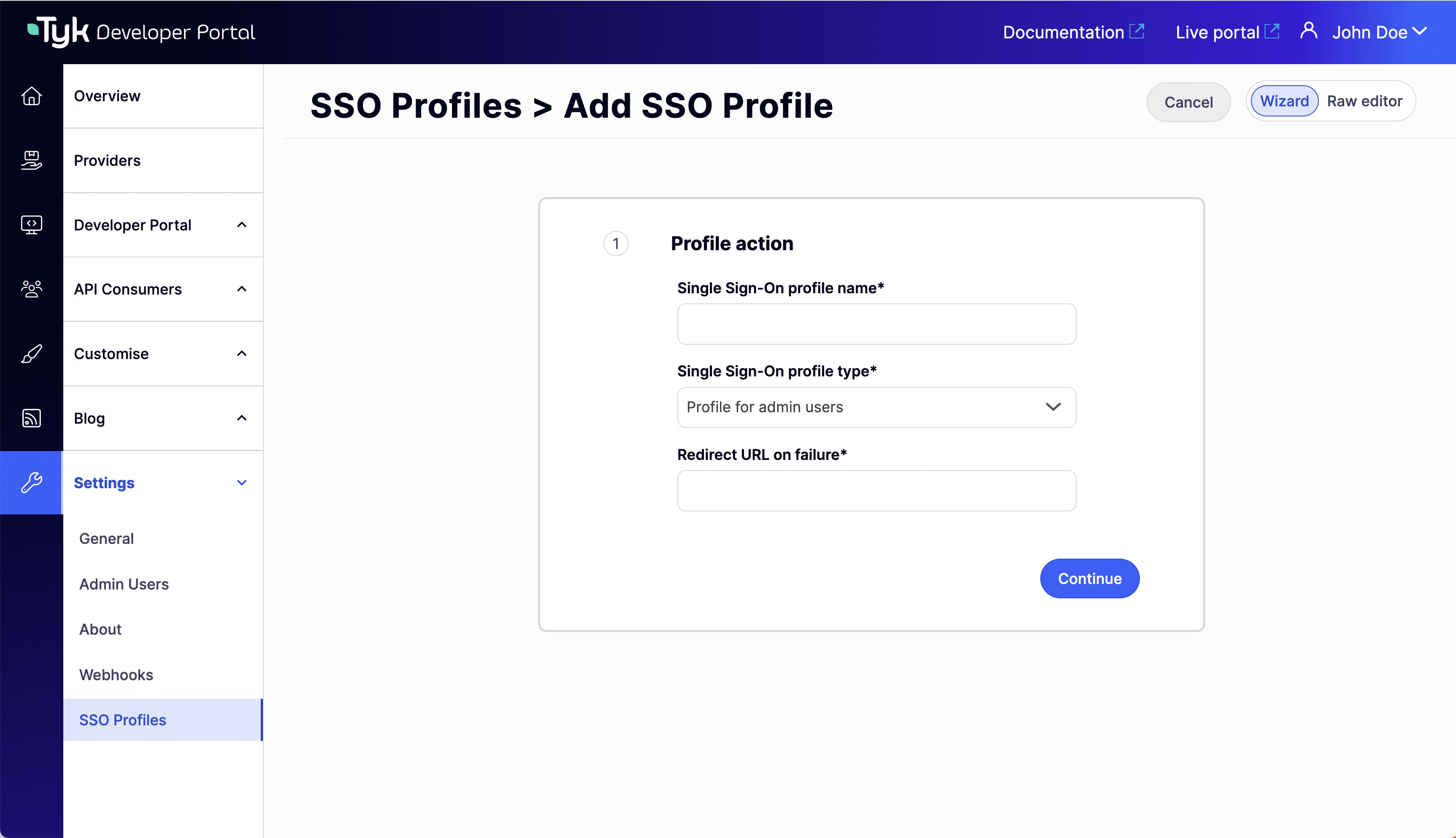
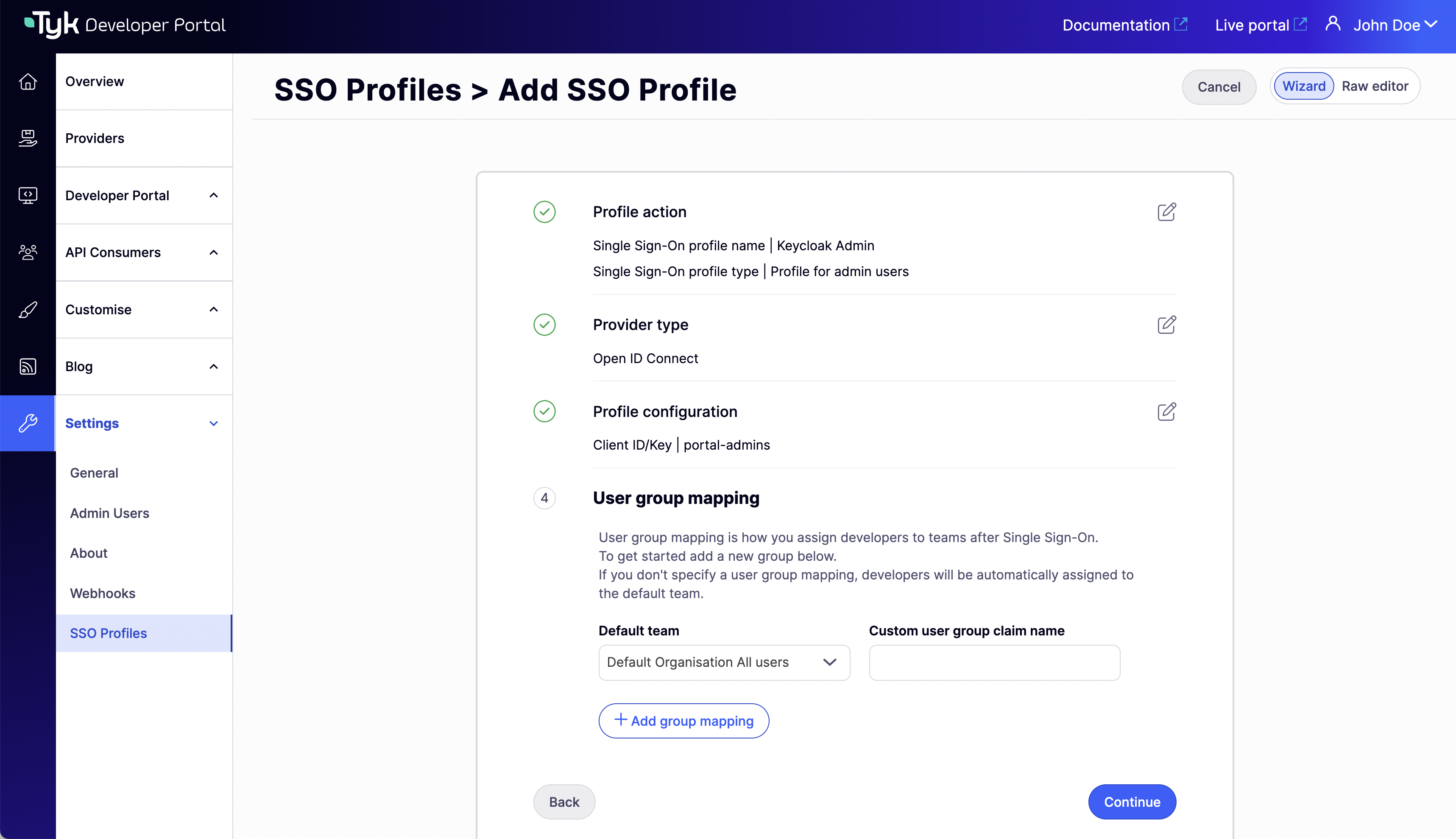
In the following sections you will learn how to configure the SSO profiles for admins and developers and map developers to the teams. You can configure the SSO profiles for admins in the Tyk Developer Portal application. Under Settings > SSO Profiles > Add new SSO Profile. There are two ways of creating SSO profiles:- Wizard Form: Create a profile using the wizard guided form.
- Raw JSON Editor: Create a profile using JSON editor where you can specify your tib raw JSON profile.
Using the Wizard Form
You can access the wizard form by switching to the Wizard view.- Profile for admins
- Profile for developers
Create a profile for admins: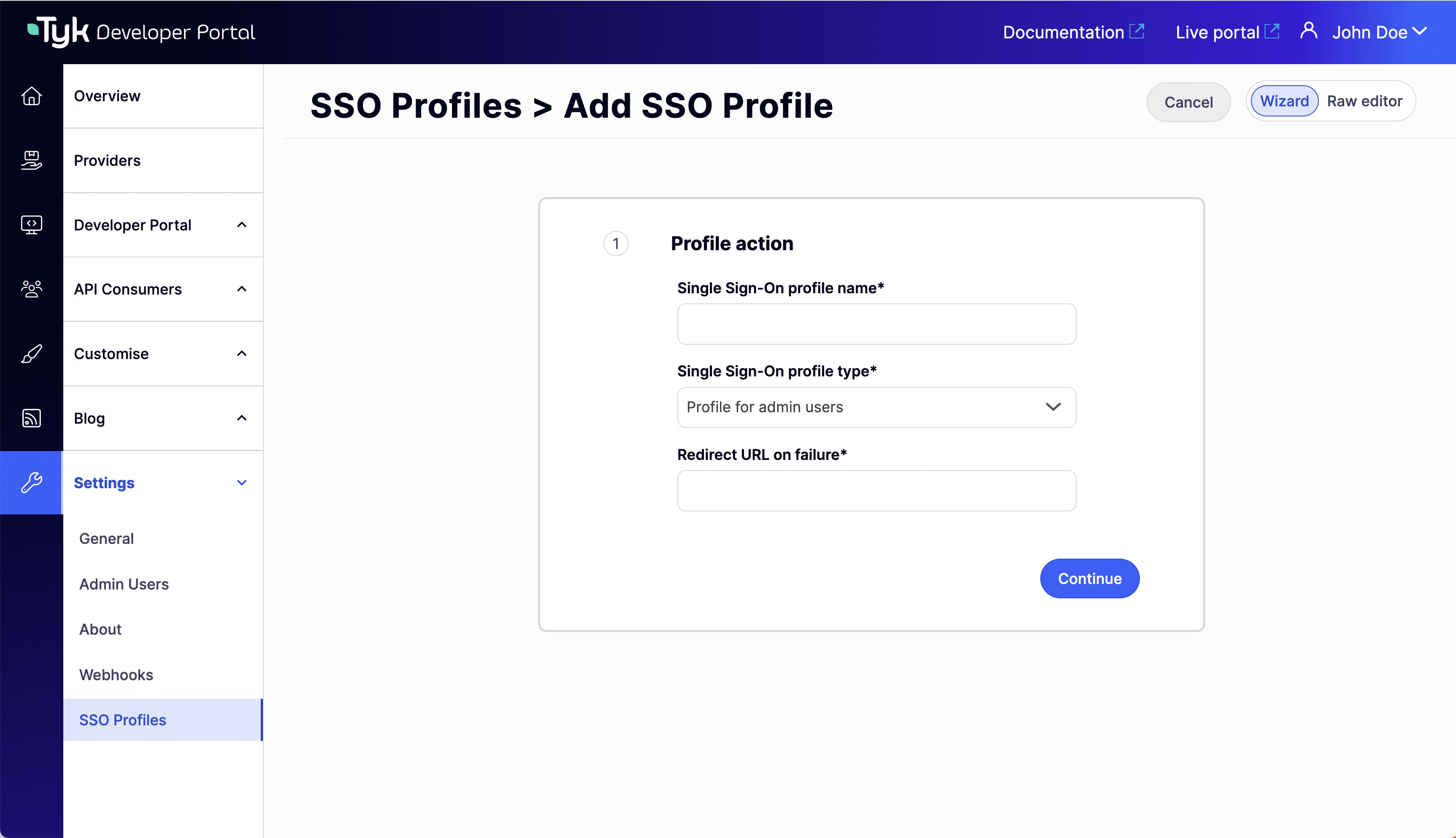
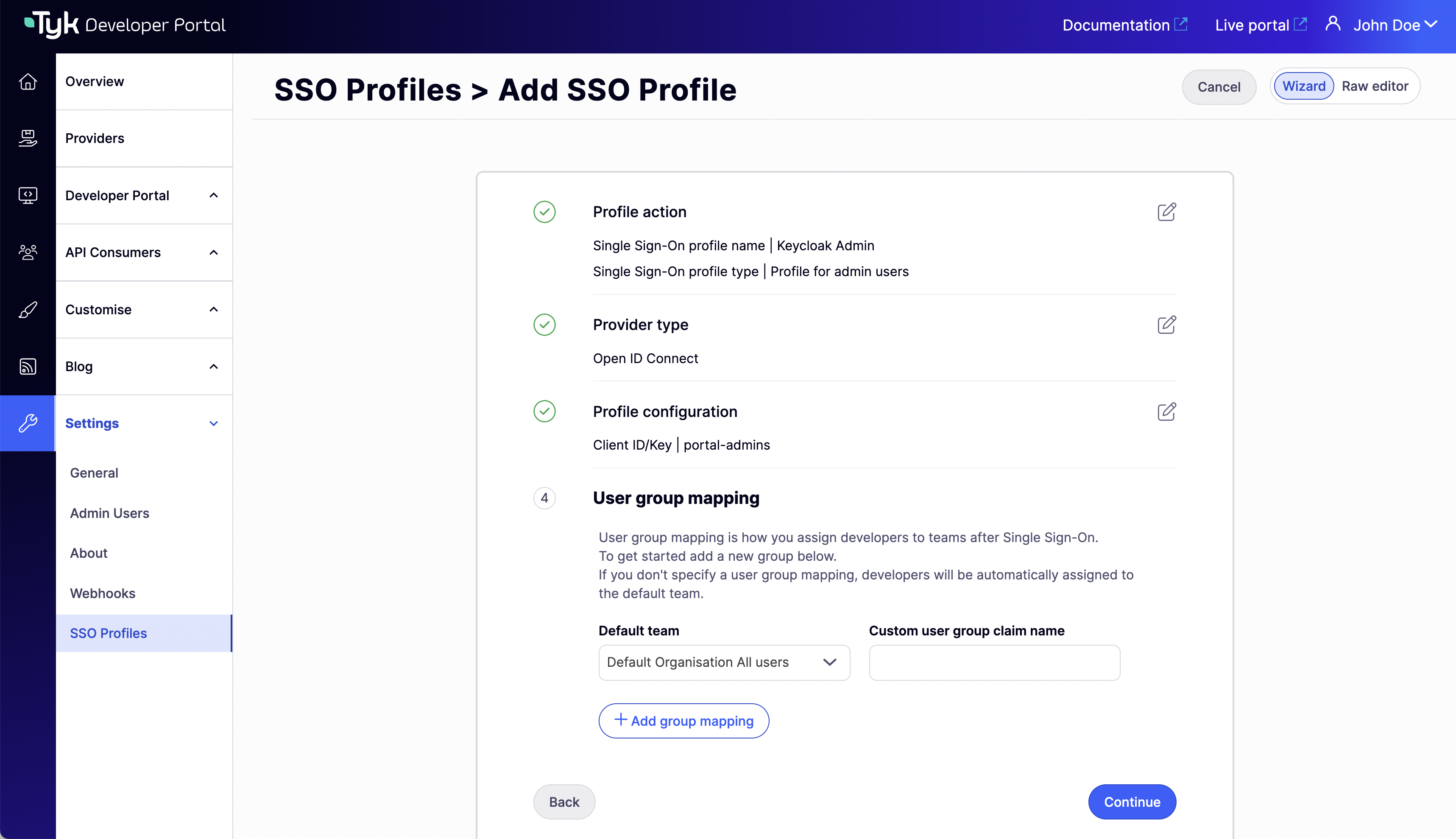
- Complete the Profile action step. Here you can choose a name (this name will generate the profile ID), the profile type (select Profile for admin users) and the redirect url on failure.
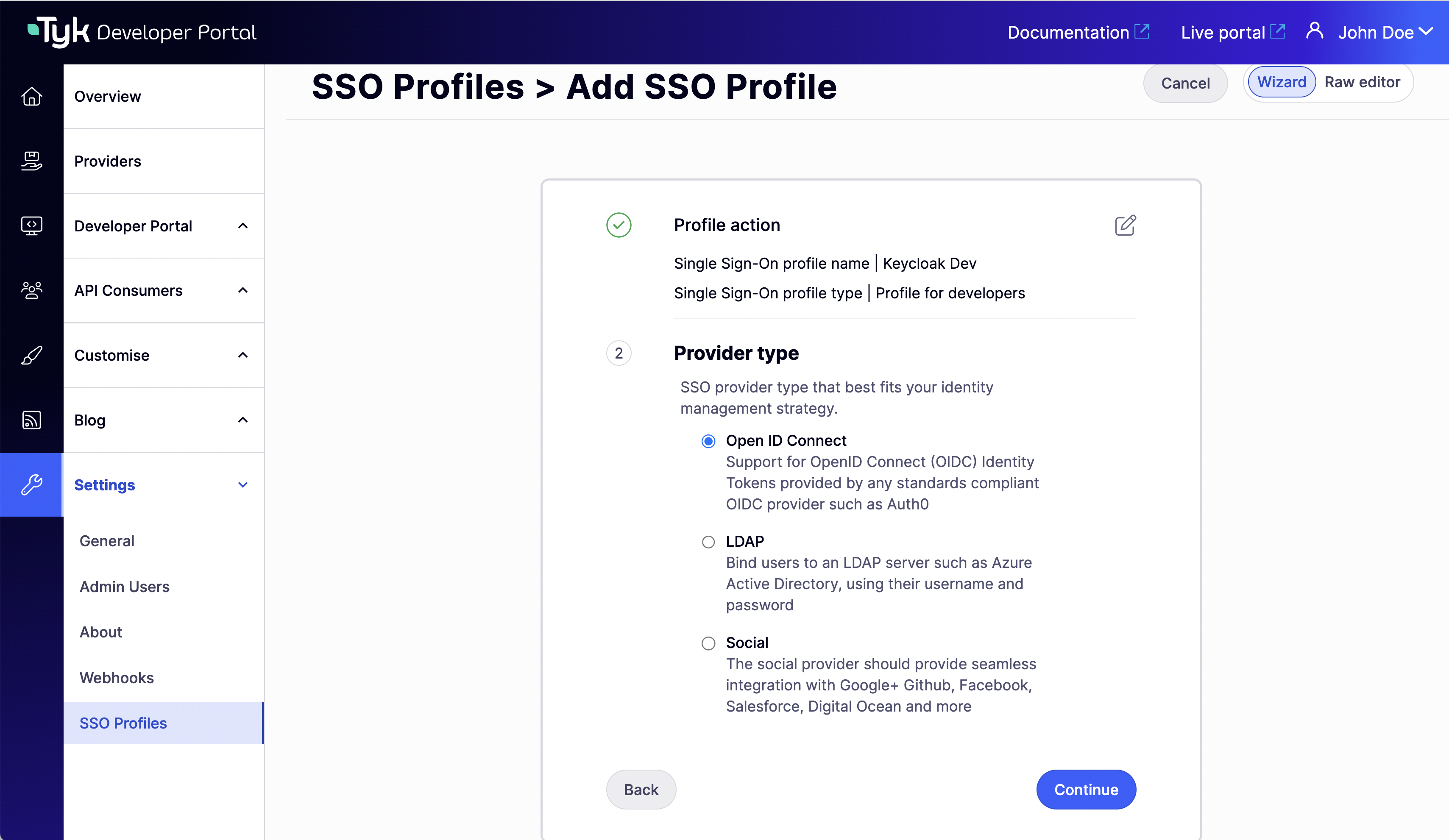
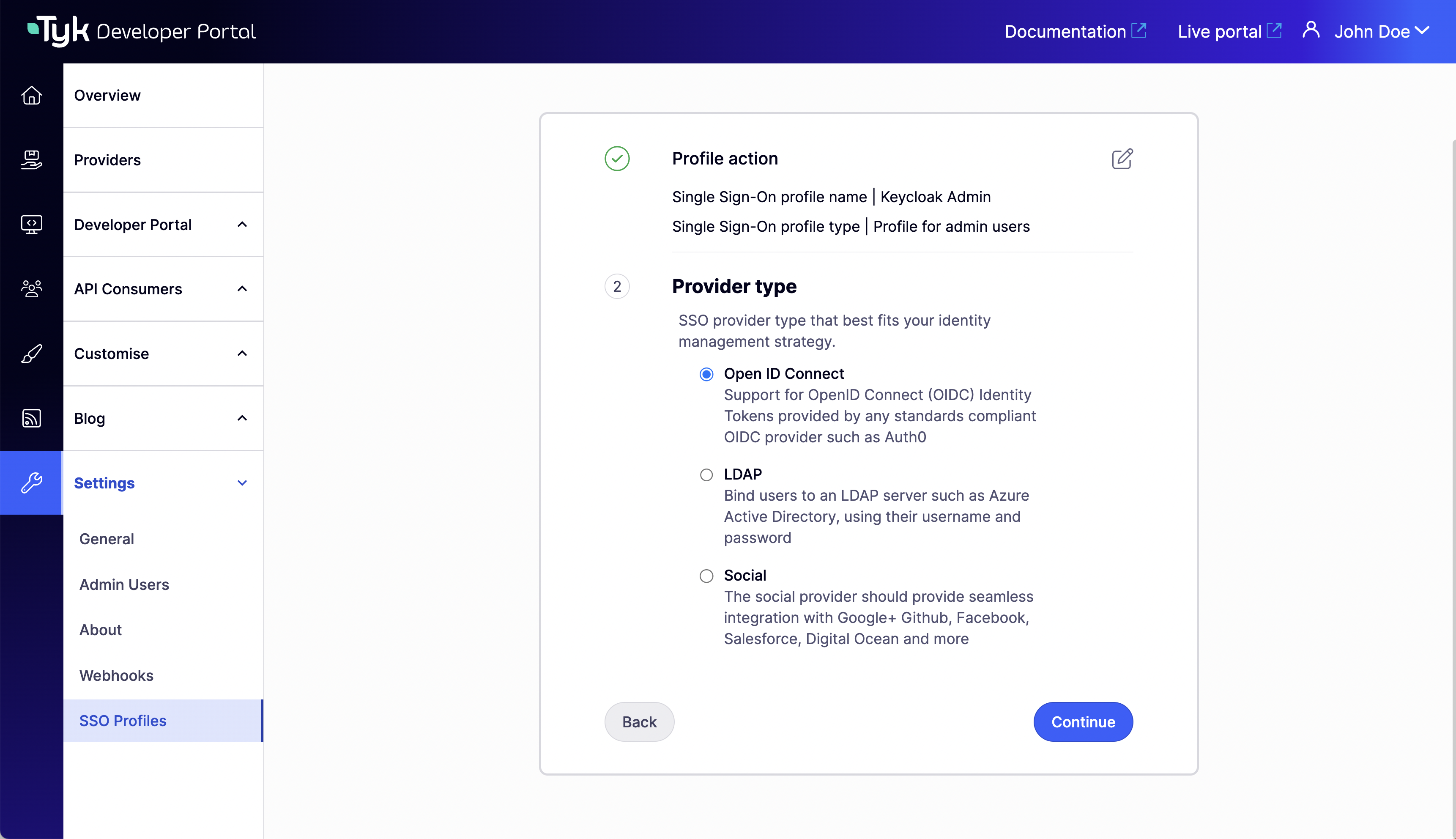
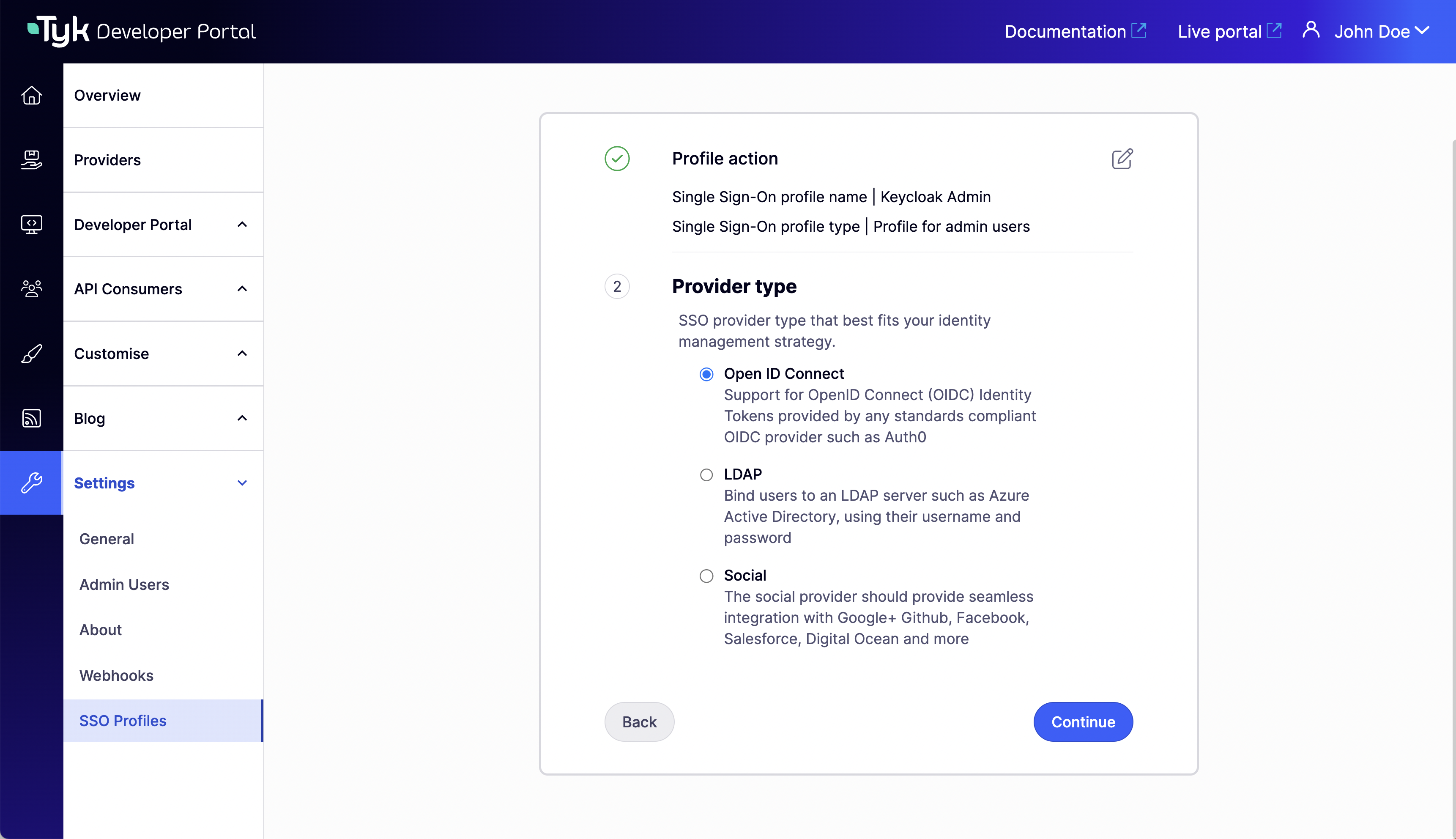
- Select a supported Provider type.
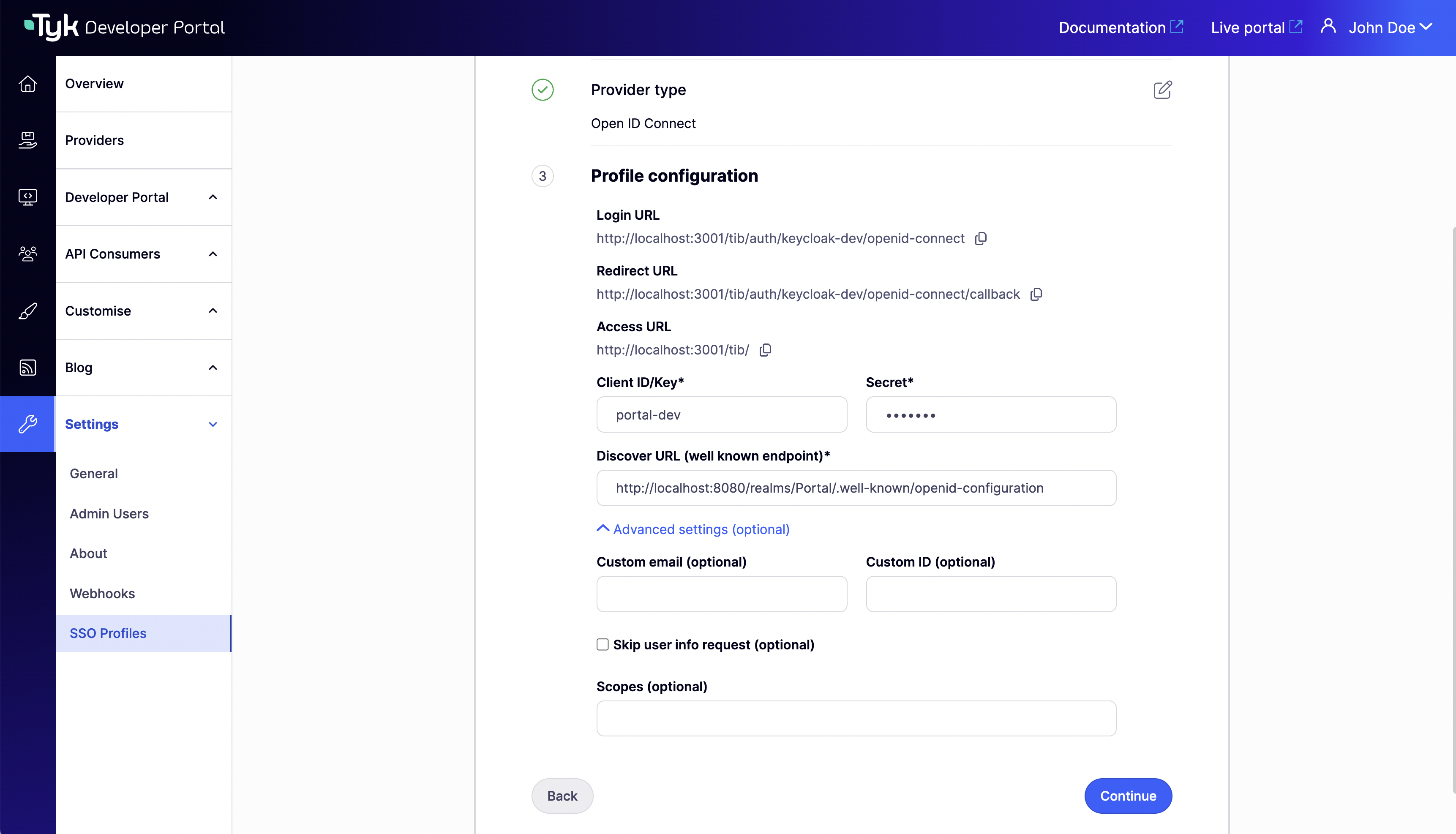
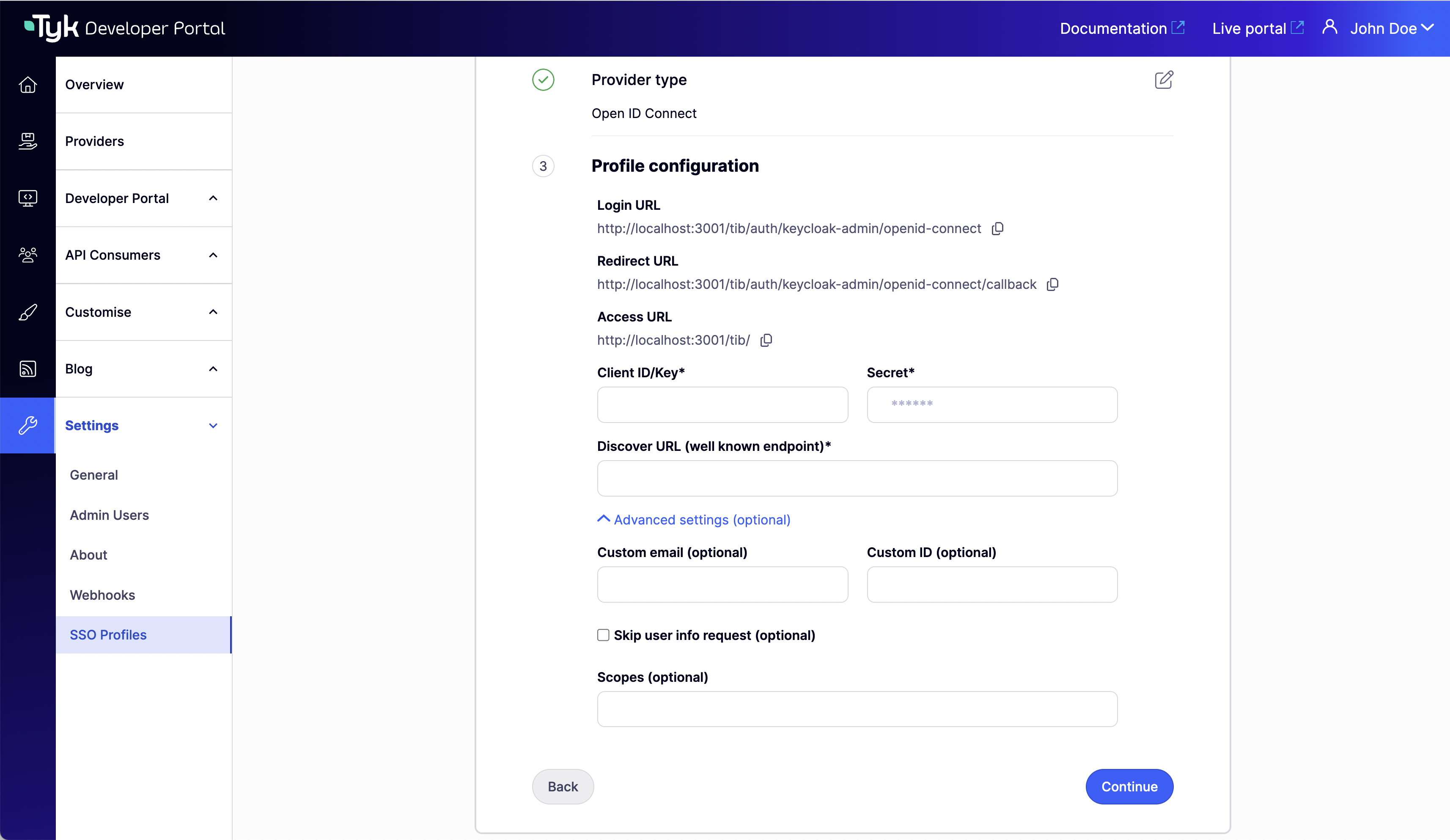
- Complete the Profile configuration step. Here you can specify the access to your idp. And Advanced settings if needed.
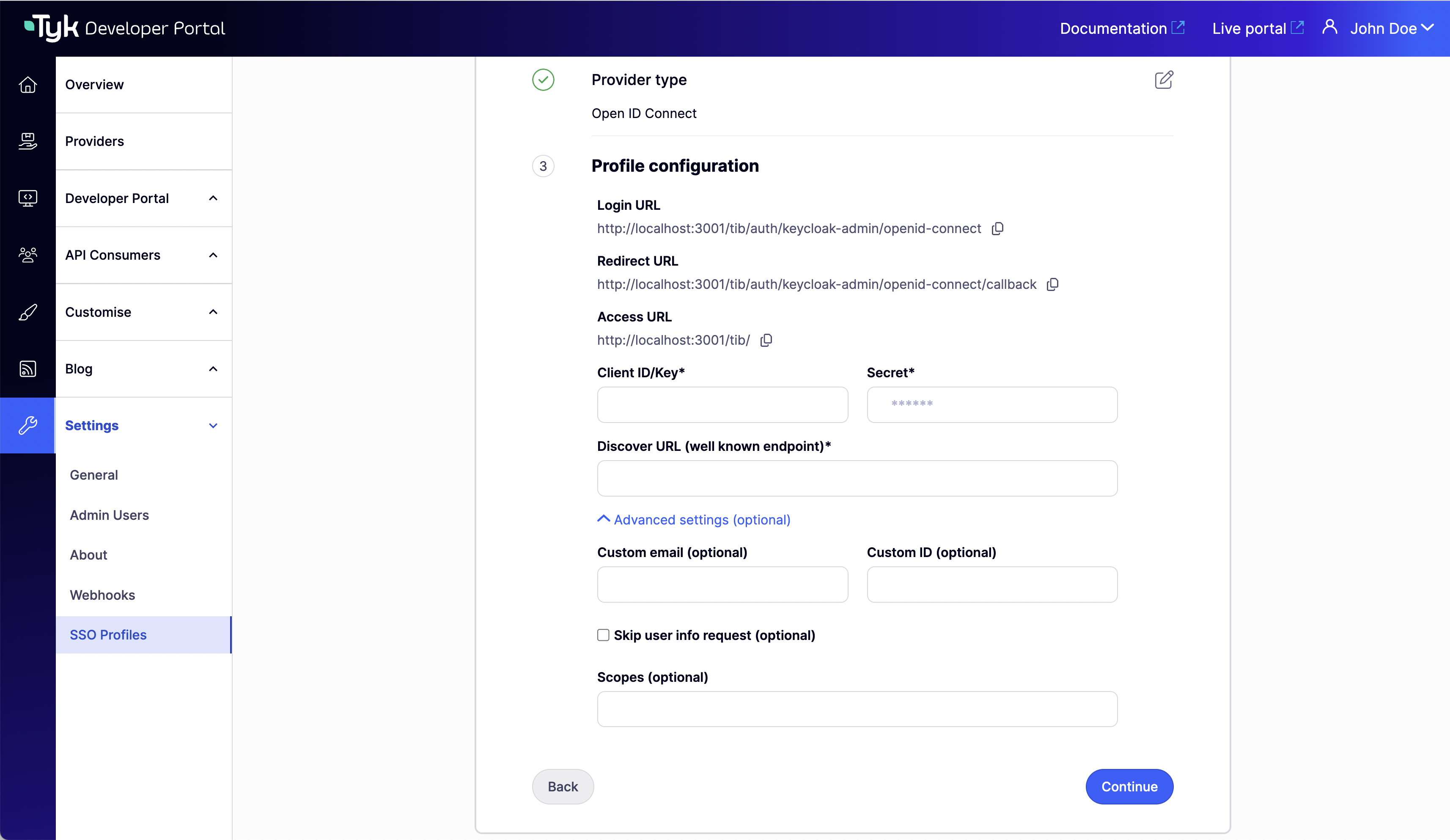
- Don’t add any group mapping since we are creating a profile for admins and will be ignored if added. Click on Continue to create the profile.
Using the JSON Raw Editor
The Tyk Identity Broker (TIB) uses profiles to define details related to the identity provider such as its type and access credentials, and instructs TIB on how to treat users that try log in with that provider. You can access the raw editor by switching to the Raw editor view, which displays a JSON editor with an empty TIB profile for guidance.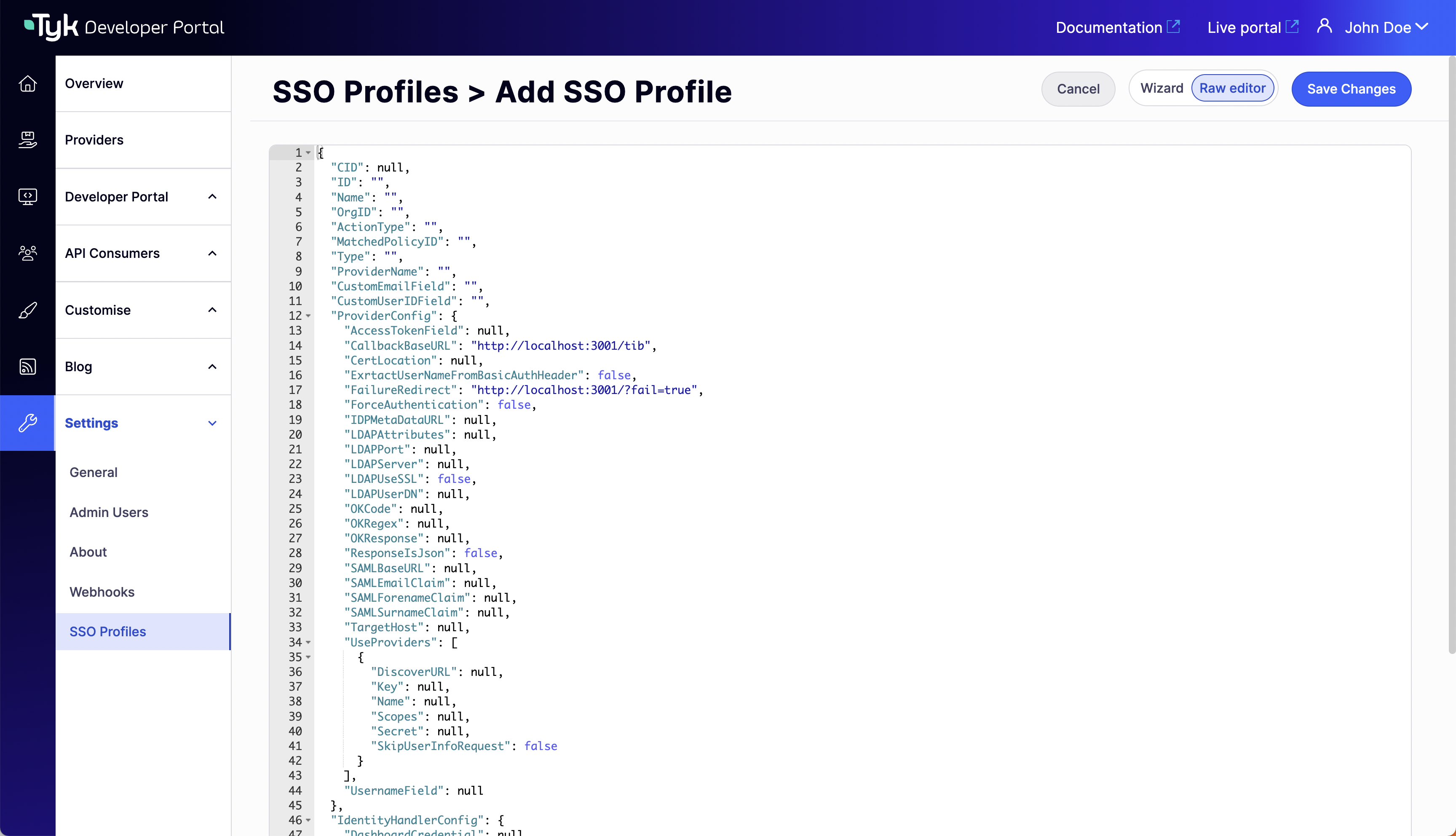
- Profile for admins
- Profile for developers
- Tab Title
- Tab Title
Create a profile for admins. Make sure the ActionType is equal to 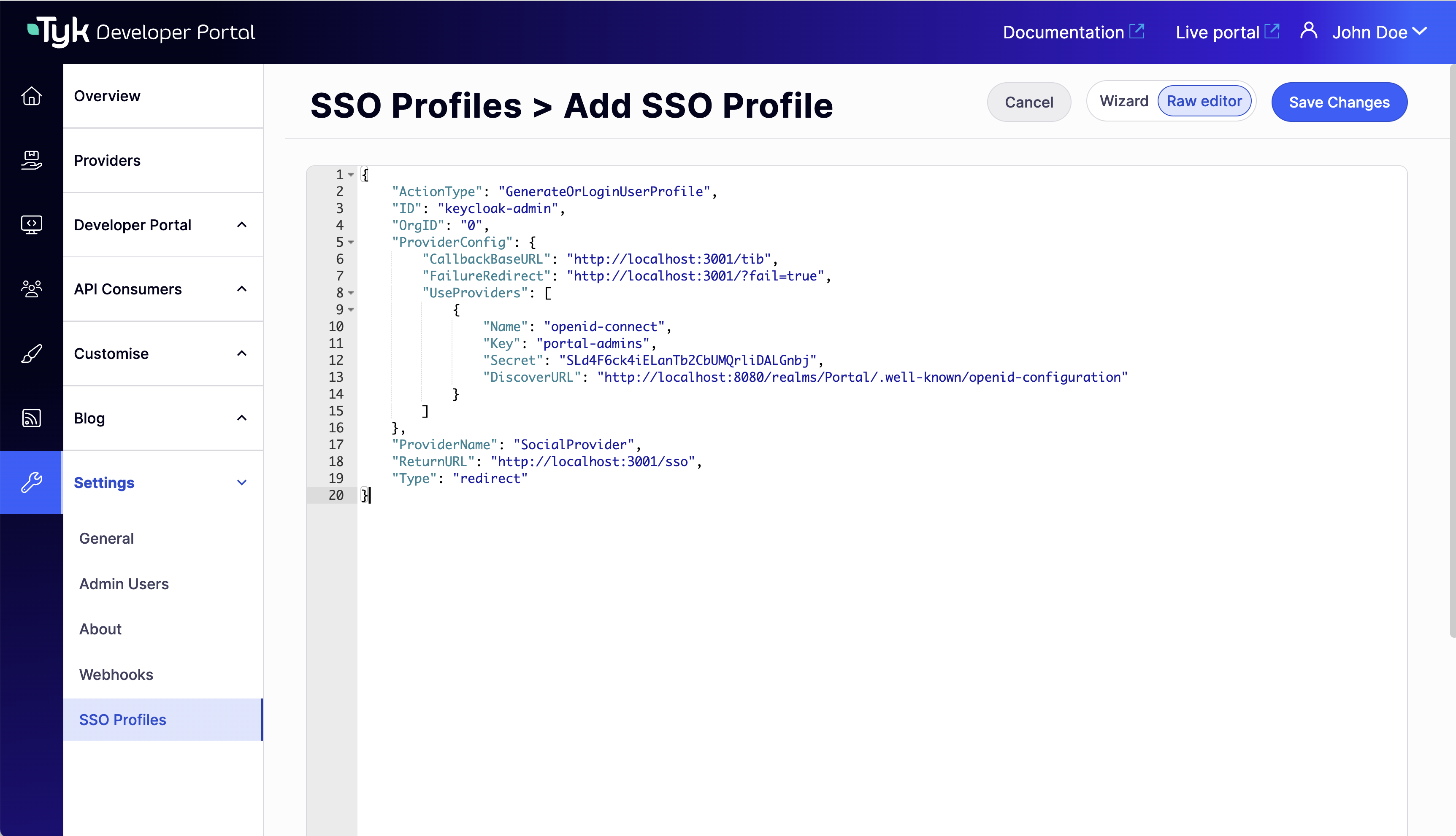
GenerateOrLoginUserProfile and the OrgID is equal to “0.”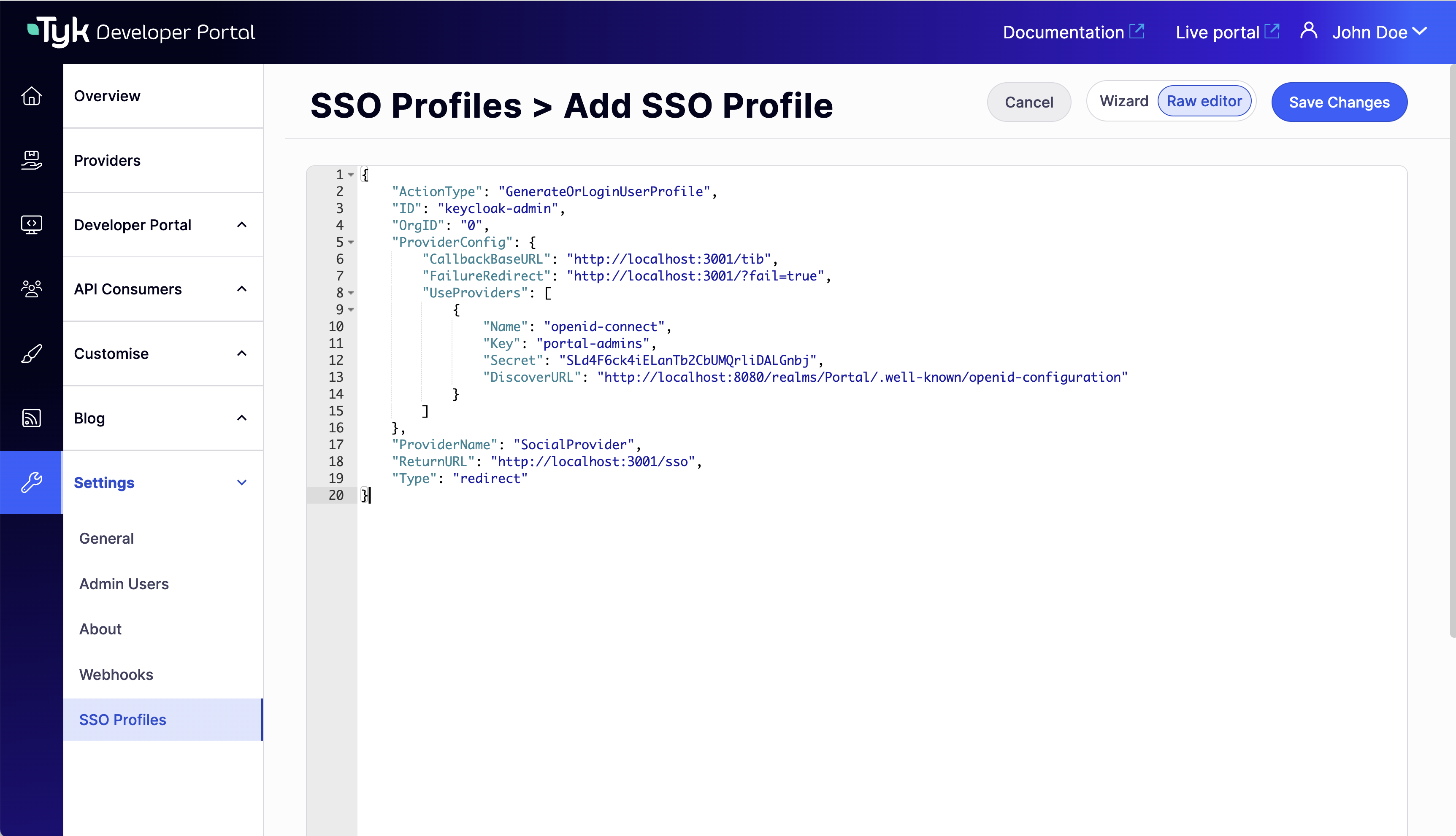
OrgIDmust be"0"for being accepted as a provider-adminActionTypemust be equal to"GenerateOrLoginUserProfile"- Replace the
hostandportin the fieldsCallbackBaseURL,FailureRedirectandReturnURLwith the actual host and port on which your portal instance is running. Also, replacehttpwithhttpsfor the respective fields if you use https for your portal instance - Replace the
hostandportin the fieldDiscoverURLwith the actual host and port on which your IDP instance is running. Also, replacehttpwithhttpsaccordingly - In the
"ID"field, specify an ID of this TIB profile. You can select any value for this field that consists of digits, letters, and special signs, no spaces allowed. It is better to pick a human-readable ID for your profile for better maintainability of the configuration
Testing SSO
You can access the login URL in your SSO Profile details Provider configuration section.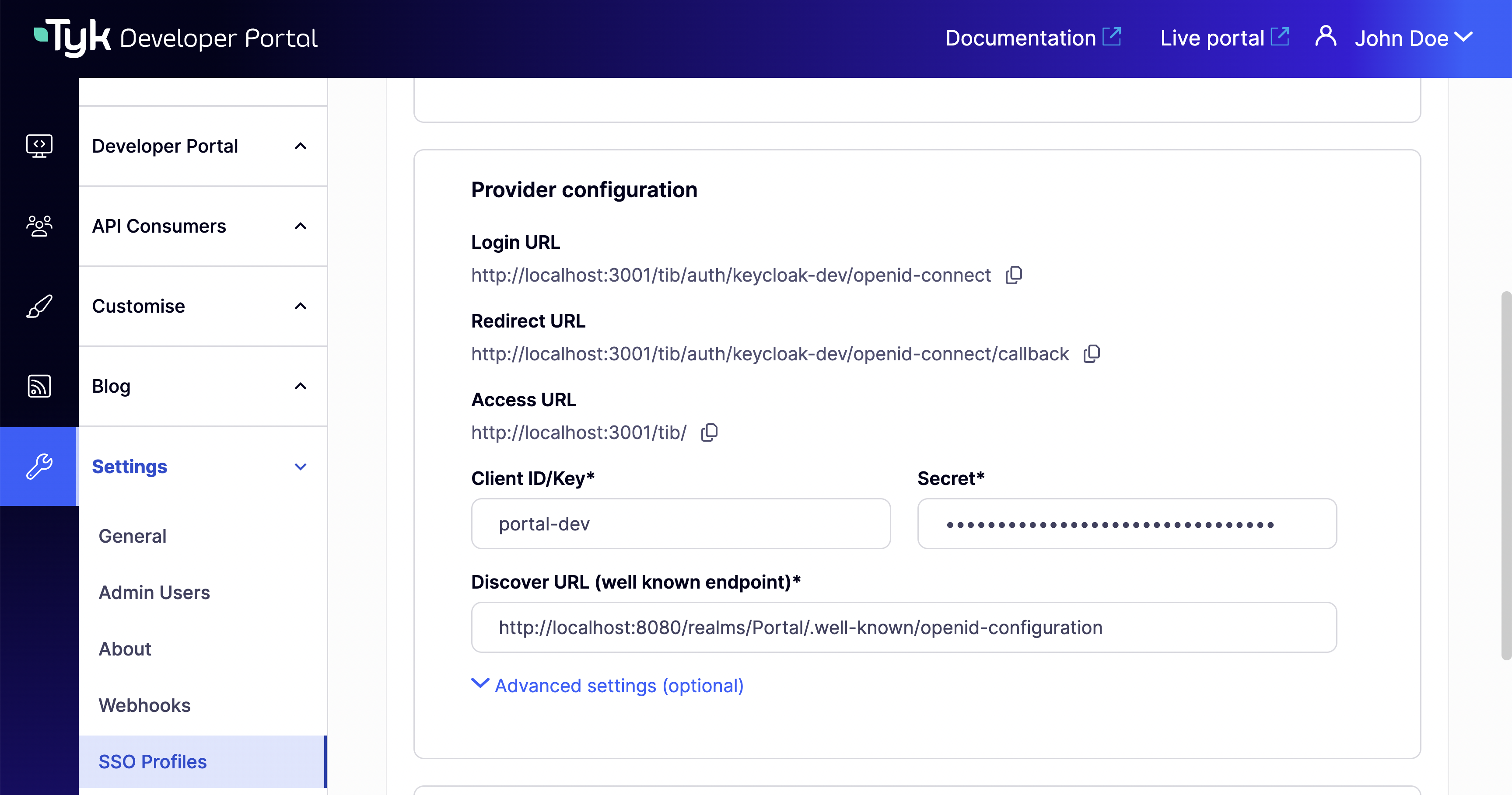
From Portal v1.16.0, you can alternatively configure a custom SSO login URL to redirect users directly to your external IdP login page without building one.
PORTAL_API_SECRET variable to the portal .env file:
PORTAL_API_SECRET to extraEnvs:
Configuring SSO with External TIB
Configure Tyk Identity Broker to work with Tyk Enterprise Developer Portal
The Tyk Enterprise Developer portal uses the Tyk Identity Broker to work with various Identity Management Systems, such as LDAP, Social OAuth (e.g., GPlus, Twitter, GitHub), or Basic Authentication providers. Therefore, to configure Single Sign-On for the portal, you need to install and configure Tyk Identity Broker first. Follow these steps to achieve this:Install Tyk Identity Broker
Please refer to the TIB installation guide documentation for different installation options:Specify TIB settings to work with the Tyk Enterprise Developer portal
Docker or packages
Create tib.conf file for the Docker installation or if you use packages to deploy TIB:- TykAPISettings.DashboardConfig.Endpoint is the Developer portal url. Pay attention if any of the elements (TIB or Portal) is running on containers.
- TykAPISettings.DashboardConfig.Port is the Developer portal port.
- TykAPISettings.DashboardConfig.AdminSecret is
PortalAPISecretin the configuration file of the Developer portal.
Helm charts
If you wish ot deploy TIB in Kubernetes via Tyk helm chart, you need to specify TIB config as extraVars:Configure Single Sign-On for admin users and developers
What is the Tyk Identity Broker profile
The Tyk Identity Broker (TIB) uses profiles to define details related to the identity provider such as its type and access credentials, and instructs TIB on how to treat users that try log in with that provider. In this guide, you will create two TIB profiles for admins users and developers. This allows you to have different identity providers for admins and developers as well as for internal and external users. Depending on your installation options for TIB, you need to specify profiles via a json file (for Docker or packages) or via a ConfigMap (for Tyk Helm Chart).profiles.json for Docker or packages installation
Here is an example of profiles.json file for Docker or packages installation:ConfigMap for Tyk Helm chart installation
Here is an example of ConfigMap for the Tyk Helm chart installation:Configure Single Sign-On for admin users
The Tyk Enterprise Developer portal has two audiences: developers and admins. This section provides guidance on implementing Single Sign-On for admin users. The configuration is rather straightforward, and you need to take these three steps to enable Single Sign-On for admin users in your portal instance:- Create a profile for the Tyk Identity Broker (TIB) to work on your identity provider. Make sure the ActionType is equal to “GenerateOrLoginUserProfile”, and OrgID is equal to “0”:
-
OrgIDmust be"0"for being accepted as a provider-admin or super-admin -
ActionTypemust be equal to"GenerateOrLoginUserProfile" -
IdentityHandlerConfig.DashboardCredentialmust be equal to thePortalAPISecretfield in the configuration file of the portal -
Replace
{portal host}and{portal port}with the actual host and port on which your portal instance is running. Also, replacehttpwithhttpsfor the respective fields if you use https for your portal instance -
Replace
{TIB host}and{TIB port}with the actual host and port on which your TIB instance is running. Also, replacehttpwithhttpsfor the respective fields if you use https for your TIB instance -
In the
"ID"field, specify an ID of this TIB profile. You can select any value for this field that consists of digits, letters, and special signs, no spaces allowed. It is better to pick a human-readable ID for your profile for better maintainability of the configurationNuances of OIDC configurationTo ensure that the portal can log in a user with your OIDC Identity provider, you may need to either explicitly specify the email scopes in a profile configuration or configure your IDP to include the email claim in the JWT. Failure to include the email scope in the JWT would result in the portal not having access to the user’s email.As an example, for Okta, you can use the following configuration:
-
Create a login page for admin users. We don’t supply a login page for Single Sign-On out of the box, so you need to create one.
From Portal v1.16.0, you can alternatively configure a custom SSO login URL to redirect users directly to your external IdP login page without building one.
- Now you should be able to log in to the portal with your identity provider as an admin user
Configure Single Sign-On for developers
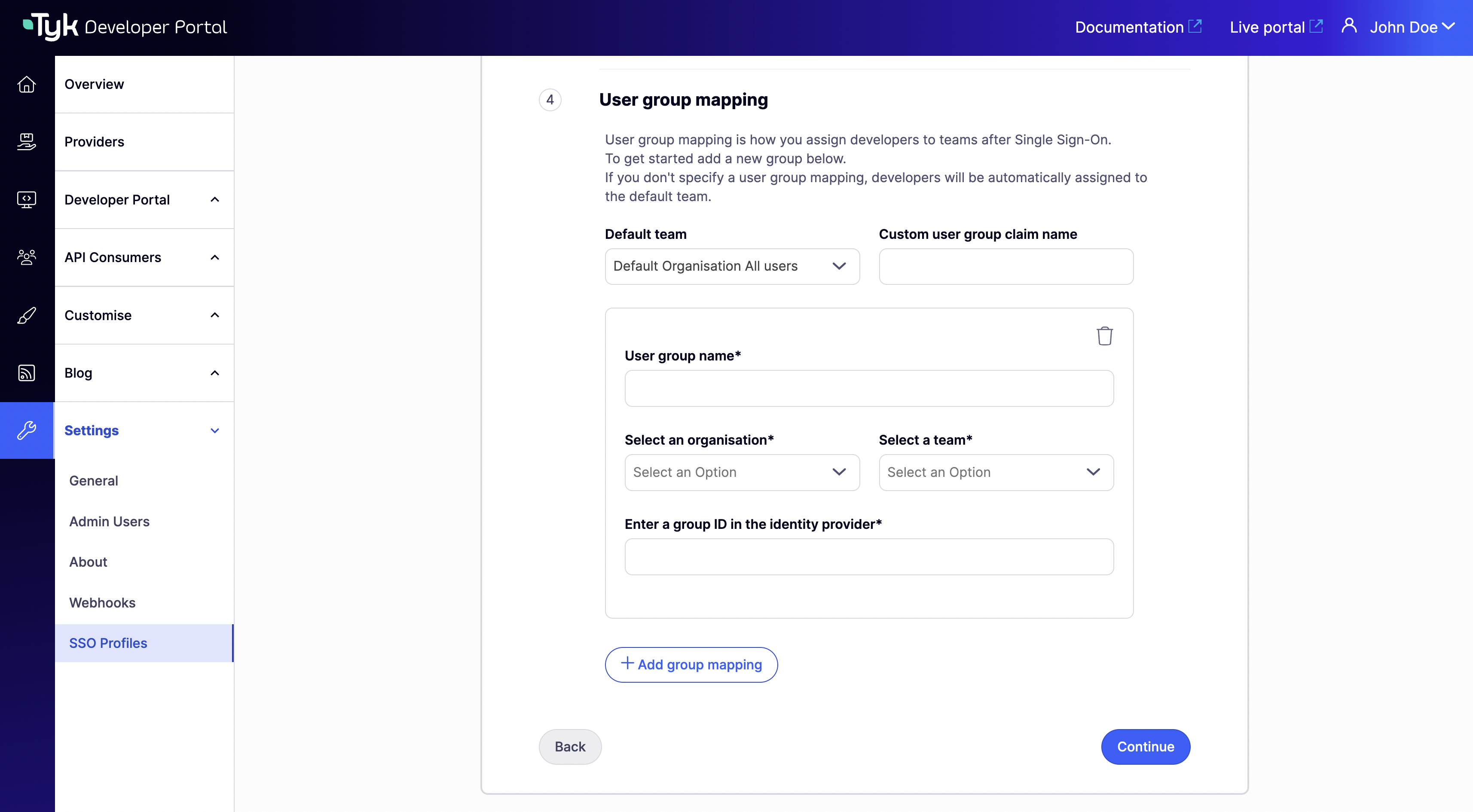
This section relates to configuration and settings required to set up Single Sign-On for developers. Configuration for developers is also straight forward. However, for developers there is one additional.User group mapping
In order to land a developer into the right API Consumer organization, it is necessary to configure the UserGroupMapping in the TIB profile that creates a binding between user groups in your IDP and developer teams in the portal.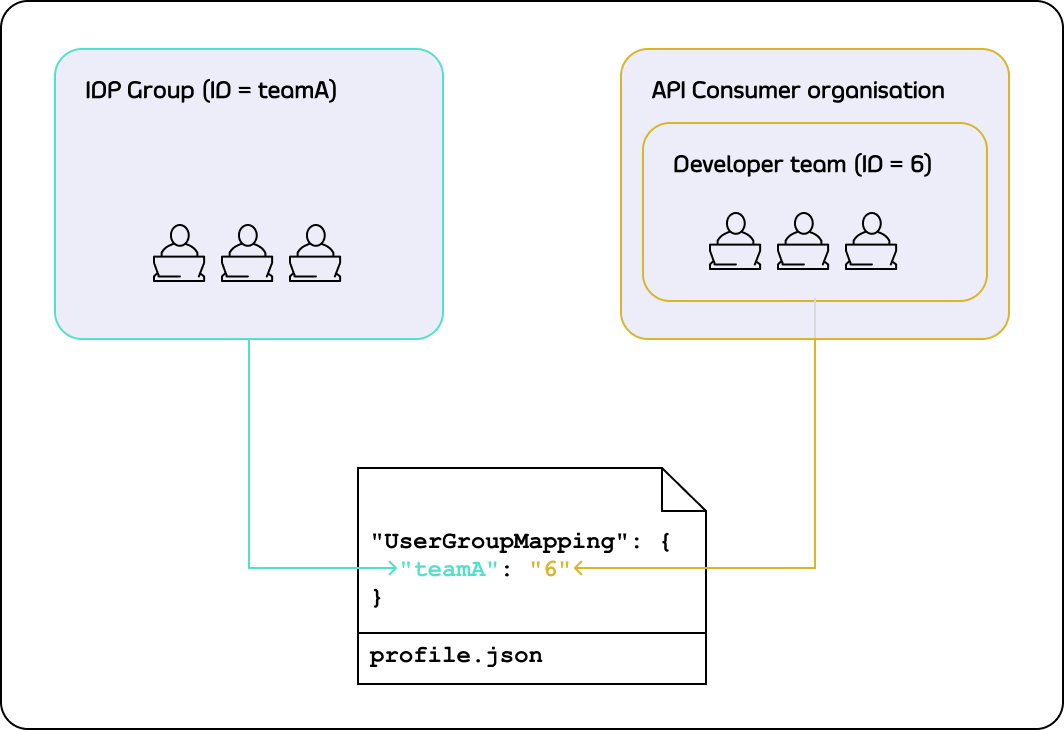
UserGroupMapping object contains keys that refer to group IDs in your IDP, and the corresponding values are team IDs in the portal.
When the Tyk Identity Broker authorizes a user, it searches for a key that matches the user’s group ID in the IDP.
If TIB can’t find a matching group ID, it logs the user in to the team with an ID equal to DefaultUserGroupID in the portal (if DefaultUserGroupID is defined).
We recommend always defining DefaultUserGroupID and ensuring that it refers to a valid team ID in your portal instance. If DefaultUserGroupID is defined but refers to an invalid team ID, the portal will refuse login attempts.
If no matching group ID is found in the UserGroupMapping object and DefaultUserGroupID isn’t defined, the portal logs in the user to the “Default organization | All users” team with an ID of 1.
To determine whether a developer should be allowed to log in and which team they should be logged into, the portal uses the following algorithm:
Configure profile to enable Single Sign-On for developers
Follow these steps to enable Single Sign-On for developers:- Create a profile for the Tyk Identity Broker (TIB) to work on your identity provider. Make sure the ActionType is equal to “GenerateOrLoginUserProfile”, and OrgID is equal to “0”:
-
OrgIDcould be anything as its value is ignored; -
ActionTypemust be equal to"GenerateOrLoginDeveloperProfile" -
IdentityHandlerConfig.DashboardCredentialmust be equal to thePortalAPISecretfield in the configuration file of the portal -
Replace
{portal host}and{portal port}with the actual host and port on which your portal instance is running. Also, replacehttpwithhttpsfor the respective fields if you use https for your portal instance -
Replace
{TIB host}and{TIB port}with the actual host and port on which your TIB instance is running. Also, replacehttpwithhttpsfor the respective fields if you use https for your TIB instance -
In the
"ID"field, specify an ID of this TIB profile. You can select any value for this field that consists of digits, letters, and special signs, no spaces allowed. It is better to pick a human-readable ID for your profile for better maintainability of the configuration -
CustomUserGroupFieldmust be equal to the JWT claim name that refers to the user group in your IDP -
UserGroupMappingan object that defines relationship between user groups in the IDP and teams in the portal. The optional parameter, if not specified, will cause the portal to rely on theDefaultUserGroupIDfield to determine which team a developer should log in to. Please refer to the User group mapping section for guidance -
DefaultUserGroupIDis the default organization that the portal will use to determine which team a developer should be logged in to if it is not able to find a UserGroupMapping for that developerNuances of OIDC configurationTo ensure that the portal can log in a user with your OIDC Identity provider, you may need to either explicitly specify the email scopes in a profile configuration or configure your IDP to include the email claim in the JWT. Failure to include the email scope in the JWT would result in the portal not having access to the user’s email.As an example, for Okta, you can use the following configuration:
- Create a login page for developers. We don’t supply a login page for Single Sign-On out of the box, so you need to create one. Here is an example of such page that works with a profile for LDAP identity management system:
- Now you should be able to log in to the portal with your identity provider as a developer
Custom SSO Login URL
Available from Portal v1.16.0. See the v1.16.0 release notes. By default, the Developer Portal renders its own login page at/auth/password/login. When you set SSOCustomLoginURL, the portal automatically redirects all login requests to the URL you specify (typically your identity provider’s login page) instead of displaying the built-in form. The Portal’s Log in button also points to this URL.
Use this setting when you want to delegate authentication entirely to an external IdP without exposing the Portal’s default login page to users.
This setting only redirects the login entry point. User registration and password reset pages are not affected.
Configuration
Set either the environment variable or the equivalent configuration file key:- Environment variable
- Config file
PORTAL_SSO_CUSTOM_LOGIN_URL in the configuration reference.