Learn the key differences between API keys and tokens, their security implications, and when to use each for optimal API authentication.
Confused by the whole API key vs token debate? Don’t be! We’re here to walk you through the differences between these two authentication modes.
API keys vs tokens: What are they?
API keys identify applications or systems accessing an API and are typically long-lived.
Tokens authenticate users and carry scoped permissions, are short-lived, and are commonly used in OAuth and session-based authentication.
If you’re looking at API auth methods, understanding the differences between API keys and API tokens is crucial. Let’s start with a quick API key definition.
Defining API keys
An API key is an alphanumeric string of code that an API server can use to identify an API caller (usually an app, device, or software module) and validate the caller’s authenticity. Its primary purpose is to identify the caller and grant access. Platform teams, for example, can use API keys to help track and rate limit integrations.
Defining API tokens
An API token – one of the most common forms of which is a bearer token – is also code-based but is usually more complex than an API key. It contains information about a user (the bearer) and their permissions, meaning an API server can not only authenticate the user but also validate their specific access privileges. This means tokens are better for developers than API keys would be in various contexts, such as user sessions.
Core components of each
An API key is a long-lived means of providing access to an API. Developers can use it to:
- Control who accesses their API
- Monitor usage
- Put a rate limiting strategy in place
- Identify APIs that are stopping an app working properl
An API token is shorter-lived and dynamically generated, either as part of an authentication flow or in response to a specific system action. It carries more data about the user and what they are permitted to do.
Quick comparison overview
In summary, an API key is used to identify and authorize the API caller, while an API token helps identify a user and validate their specific permissions. An API key is handy for public data and third-party access use cases, while API token authentication is better for temporary user authentication and sessions (including multi-factor authentication, fine-grained access control and as part of OAuth flows).
| Aspect | API keys | Tokens |
| Purpose | Identify an API client | Authenticate a user |
| Lifespan | Long-lived | Short-lived |
| Permissions | Broad | Fine-grained |
| Typical use | Public or server-to-server APIs | User sessions, OAuth, SSO |
| Security level | Lower | Higher |
Key differences and characteristics
With API key meaning taken care of, let’s look at the differences between a key and an API security token.
Generation methods and lifecycle
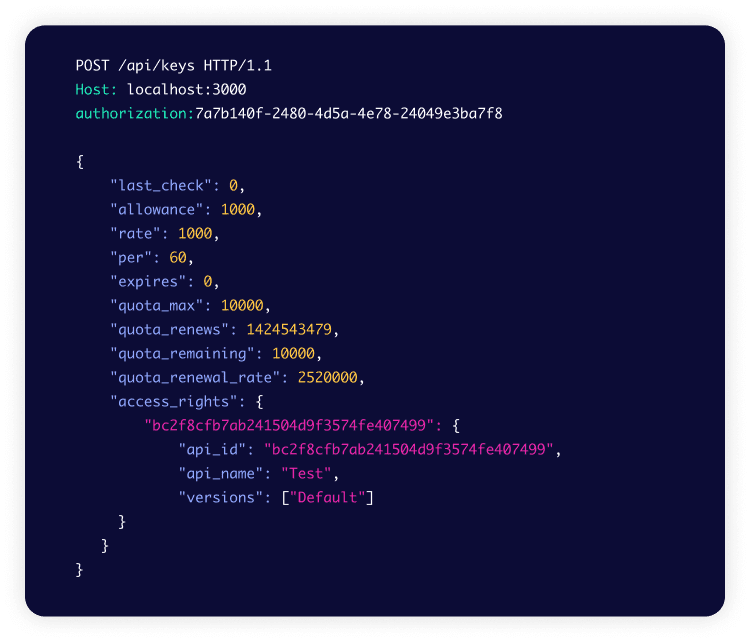
An API key is a static alphanumeric string that tends to be long-lived (though it can be set to expire). It is usually generated via an admin interface or developer portal. The image below shows how to generate an API key using Tyk Dashboard. You can also watch how to generate an API key in this video.
An API token is generated dynamically as part of an auth flow or specific action. Tokens tend to be short-lived, easy to revoke and easy to refresh. They are commonly used in OAuth 2.0-based authentication flows and often implemented as JSON Web Tokens (JWTs), as defined by industry standards. You can enable bearer tokens as part of your API definition for easy generation. The image below shows how to do this in Tyk Dashboard.
Structure and format
We notice clear differences when looking at API key vs bearer token (or other kind of API token) structure and format. An API key is simply an alphanumeric string. An API token is more structured, often containing a header, payload, and signature.
Scope and permissions
Bearer token vs API key scopes and permissions are distinctly different. An API key’s scope is to identify an API caller and permit them access. An API token’s scope is broader, with permissions linked to user roles. A token’s scope may also cover multiple APIs, such as in the case of single sign-on (SSO) tokens granting users permission to access numerous domains. However, as a token’s scope tends to be less broad than that of an API key, the damage that it can cause if the credential leaks tends to be smaller – a win for security teams.
Duration and expiration
API keys have longer durations than API tokens, though both can be set to expire. Keys usually remain in place until rotated or revoked, while access tokens usually expire after a brief time period.
Storage and management
The way in which you store and manage API keys and tokens has important security implications. Keeping API keys out of code repositories and application source trees is essential for protecting against unauthorized access. Secure storage solutions can include dedicated secrets management services and environment variables, along with encrypted databases.
For API security token storage, browser in-memory or local storage solutions can both work, depending on your application.
Security implications
There’s plenty to think about when it comes to API security best practices. A single misstep has the potential to cause major reputational and financial loss. For API key vs token security, there are numerous considerations.
Security considerations for API keys
API keys grant broad access to your APIs/data, so defending against compromise is paramount. Your observability strategy plays a crucial role in this defense, so if you’re not yet familiar with what OpenTelemetry is, now could be a good time to learn!
Remember: API keys are there to identify callers – they should never be used as a standalone security measure, but as one element of a comprehensive security solution.
Other security considerations for API keys include:
- Periodic rotation
- Restricting which keys are usable for which APIs
- Deleting any keys that are no longer needed
Security considerations for tokens
As API tokens are used to control access, they are more security-focused than API keys, with more granular security controls. Their short-lived nature and the fact they are easy to revoke, combined with the fact that each token only defines a single user’s permissions, means that compromised tokens are usually less worrying for security teams than a compromised API key.
Risk assessment
When assessing API security risks, it’s vital to consider how to protect the integrity and confidentiality of your APIs and data. This includes understanding your authentication methods, including the use of API keys and tokens. The API key vs token debate highlights different approaches to secure authentication, and it’s crucial to learn the best practices for each.
Consider your full authentication flow, including encryption, error handling, rate limiting, and input validation, and remember to think about security for both data at rest and data in transit. Choosing the optimal method, whether it’s using API keys or tokens, depends on your specific needs.
Handling compromised credentials
If an API key has been compromised, you will need to revoke it and create a new key to use in its place. The same applies with an API security token. While this takes care of the situation in technical terms, security teams will also need to dig into the impact of the compromised credentials and follow any relevant regulatory procedures in terms of reporting the breach.
Best practices for secure storage
API key vs access token storage is an important consideration. Secure storage is your best defense against unauthorized access. Using environment variables or dedicated secrets management services is good practice for API keys, while browser local storage and browser in-memory can work for secure token storage.
In terms of secure storage best practices:
- Never add sensitive data to the payload
- Never send anything over non-HTTPS connections
- Rotate API keys periodically
- Ensure tokens have a set expiration time
- Provide regular security training for your team
When to use API keys
API keys confirm an API caller’s identity, so have numerous use cases.
Ideal use cases
The ideal use case for an API key is a scenario in which you need to grant long-lived access to the entirety of your API and want to identify the applications that are calling it. Example use cases include:
Server-to-server communication
API keys can ensure communication only flows between permitted servers and apps. If the API server doesn’t recognize a key, it won’t grant access.
Third-party integrations
When you want to encourage third-party integrations of your API while retaining the ability to monitor usage (with rate limiting and monetization in mind) and troubleshoot integrations.
Public API access
API keys are often used to provide access to public data (such as weather APIs), making this an important use case for an API key (vs token).
Limitations and considerations
Remember that an API key is not a standalone security solution and should not be used as such. It is part of your wider API security strategy.
When to use tokens
Using an API token vs API key also has clear use cases.
Authentication scenarios
API tokens provide a security-focused means of authenticating users for your apps, websites, and services. By granting temporary access to resources and defining the user’s permissions, they enable the user to achieve what they need while only allowing access to the data you choose.
User sessions
When considering API authentication, understanding the differences between API keys vs tokens is essential. You can define the expiration period for your tokens, allowing you to tailor the best practice to your application’s needs, ensuring user sessions last the right amount of time.
Single sign-on (SSO)
Using tokens for SSO makes life easier for developers as well as users. You can use strong authentication methods and help prevent the reuse of passwords across different services, thus boosting security. SSO can also make account administration easier while enhancing the user experience.
OAuth and JWT implementation
JSON web tokens (JWTs) are often used for stateless authentication. Many OAuth implementations use JWTs, combining the robustness of OAuth with JWTs’ secure encoding of user information.
Benefits and trade-offs
API tokens can deliver fine-grained access control as part of your authentication flow. They are more secure than API keys and suit a variety of use cases.
Common misconceptions about API keys and tokens
API keys and tokens serve different security functions, yet developers frequently confuse their purposes. API keys identify applications; tokens authenticate users. Understanding these distinctions prevents security vulnerabilities and improves API architecture.
API keys are not authentication
API keys identify the calling application, not the user. They answer “which app is calling?” rather than “who is calling?”.
Why this matters:
- API keys lack user context and cannot verify identity
- Stolen API keys grant full application-level access
- User-specific permissions require separate authentication mechanisms
Correct approach: Combine API keys with OAuth 2.0 or JWT tokens for user authentication. API keys handle app identification; tokens handle user verification.
Tokens do not eliminate HTTPS requirements
Tokens secure the authorization layer, not the transport layer. Without HTTPS, attackers can intercept tokens through man-in-the-middle attacks.
Why this matters:
- Tokens transmitted over HTTP are visible in plain text
- Session hijacking can occur when tokens are intercepted
- Encryption at rest differs from encryption in transit
Correct approach: Always enforce HTTPS for all API communications. TLS encryption protects tokens during transmission, regardless of token type.
API keys and tokens work together in layered security
Security layers complement each other; they do not replace one another. API keys, tokens, and HTTPS all address different attack vectors.
Layered security model:
- HTTPS encrypts data in transit
- API keys identify and rate limit applications
- Access tokens authenticate users and authorize actions
- Refresh tokens maintain sessions without re-authentication
Correct approach: Implement defense in depth. Each layer mitigates threats the others cannot address.
API keys are secrets that require protection
API keys are credentials, not public identifiers. Exposed keys enable unauthorized access, quota theft, and data breaches.
Common exposure points:
- Client-side JavaScript code
- Public GitHub repositories
- Unencrypted configuration files
- Browser network logs
Correct approach: Store API keys in environment variables or secrets management systems. Never embed keys in client-side code or version control.
Tokens expire by design
Token expiration is a security feature, not a flaw. Short-lived tokens limit damage from compromised credentials.
Why tokens expire:
- Reduces window of opportunity for using stolen tokens
- Forces re-authentication to verify continued access rights
- Enables permission updates without manual revocation
Typical token lifespans:
- Access tokens: 15 minutes to 1 hour
- Refresh tokens: Days to weeks
- API keys: No automatic expiration (requires manual rotation)
Correct approach: Implement refresh token flows. Use short-lived access tokens with longer-lived refresh tokens to balance security with usability.
Conclusion
We’ve looked in detail at the whole API key vs token debate, covering everything from key differences to security and use cases. You can now move forward with confidence in terms of how best to implement and manage your auth flows.
Next steps
We’ve touched on OAuth as part of the whole API token vs API key debate. Why not explore in detail what OAuth is and how you can benefit from embracing it?