- A developer signs up and creates a Dynamic Client Registration provider using your Developer Portal.
- Tyk sends the Dynamic Client Registration call to your . The IDP replies with the client ID and secret.
- Using that information, the developer (or the application) triggers a call to the token endpoint of the IDP.
- Your developer (or the application) then triggers a call to Tyk, using the token that was generated by the IDP. Tyk validates this token using the provided by the IDP.
Requirements
- A Gluu installation, more details here.
- A Tyk Self Managed installation (Gateway + Dashboard).
Getting started with Gluu
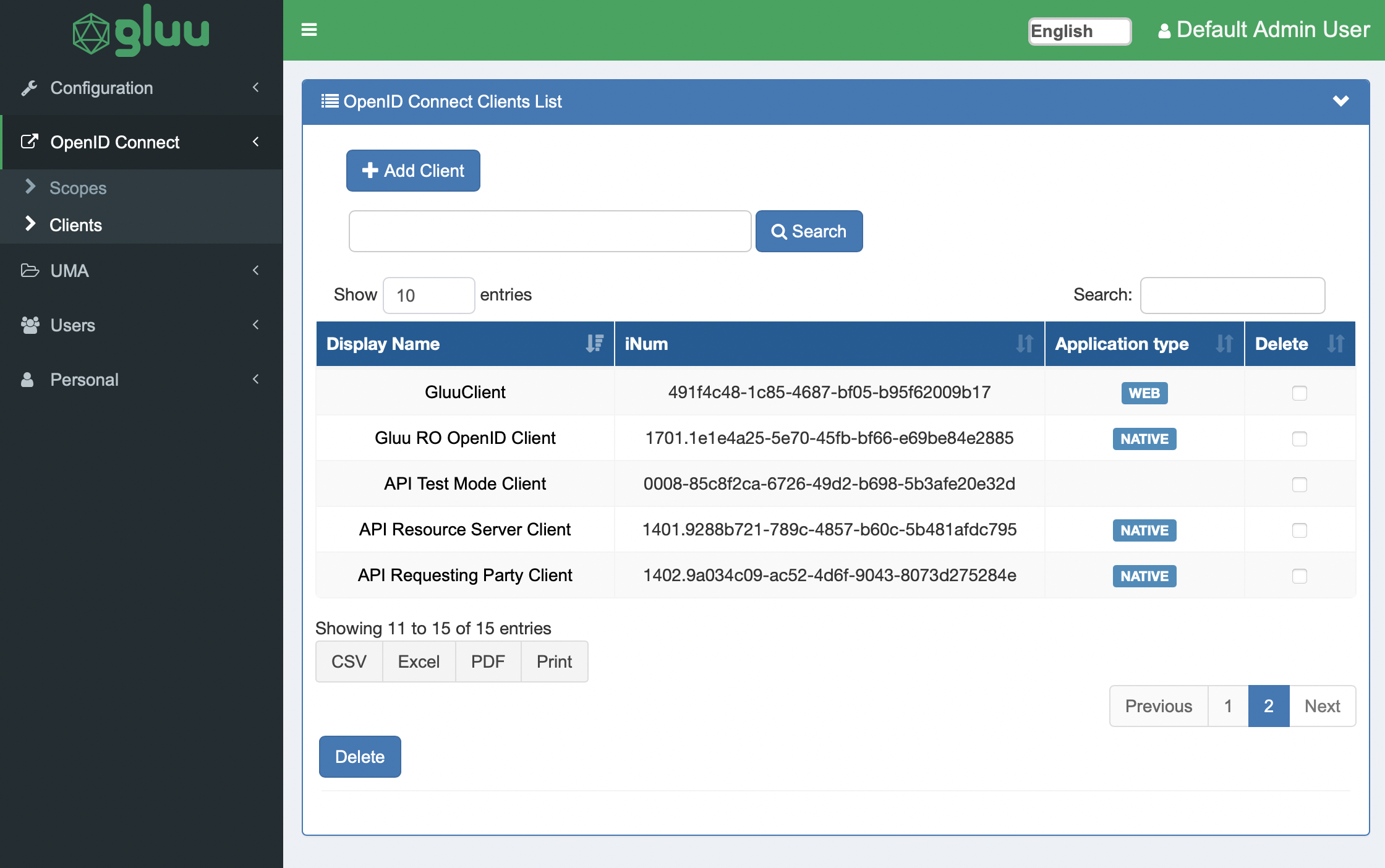
In order to get started with Dynamic Client Registration you’ll need to get the OpenID Connect registration endpoint. Open your Gluu dashboard and select the “Configuration” section. Select “JSON Configuration” and toggle the “OxAuth Configuration” tab.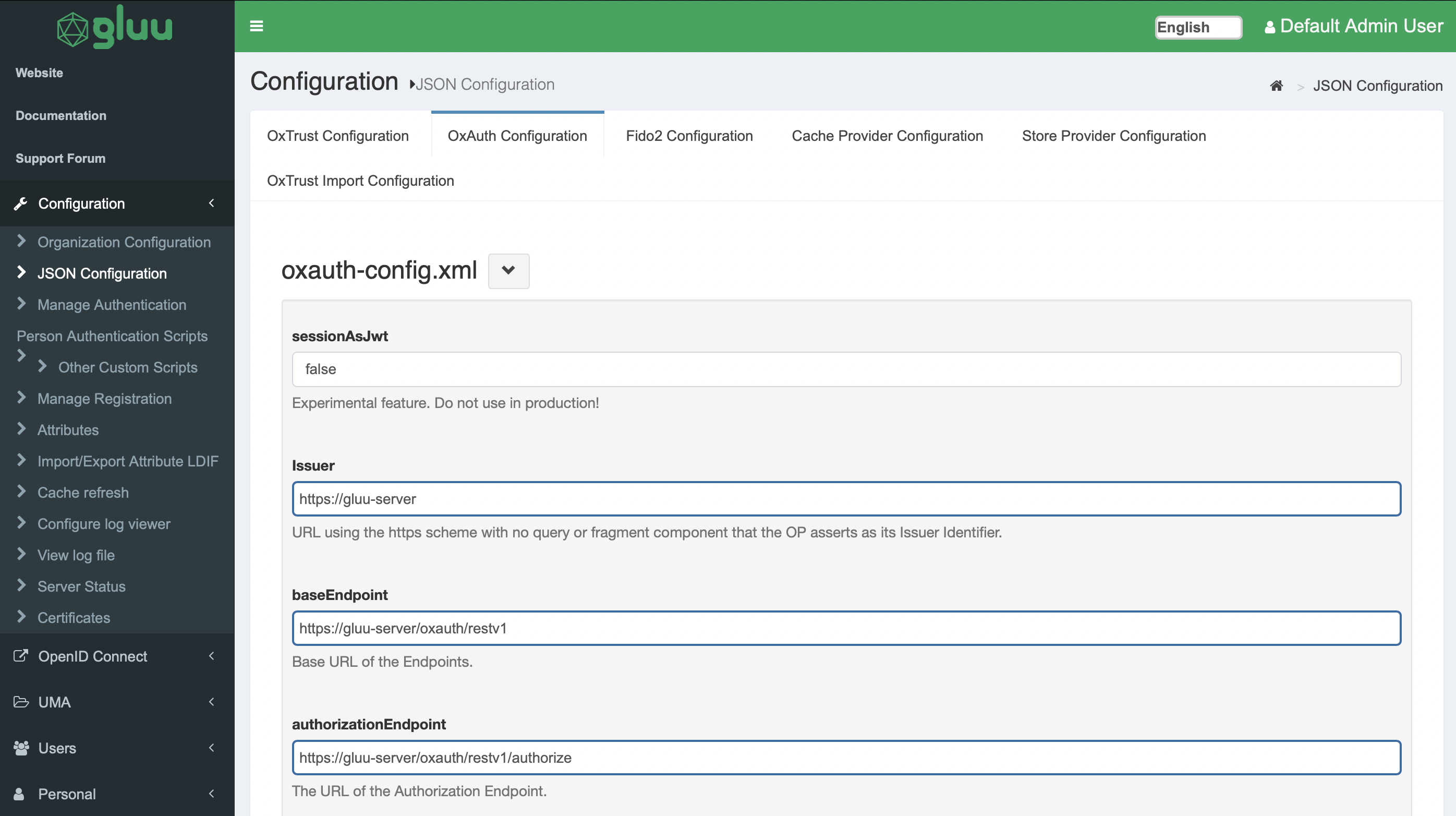
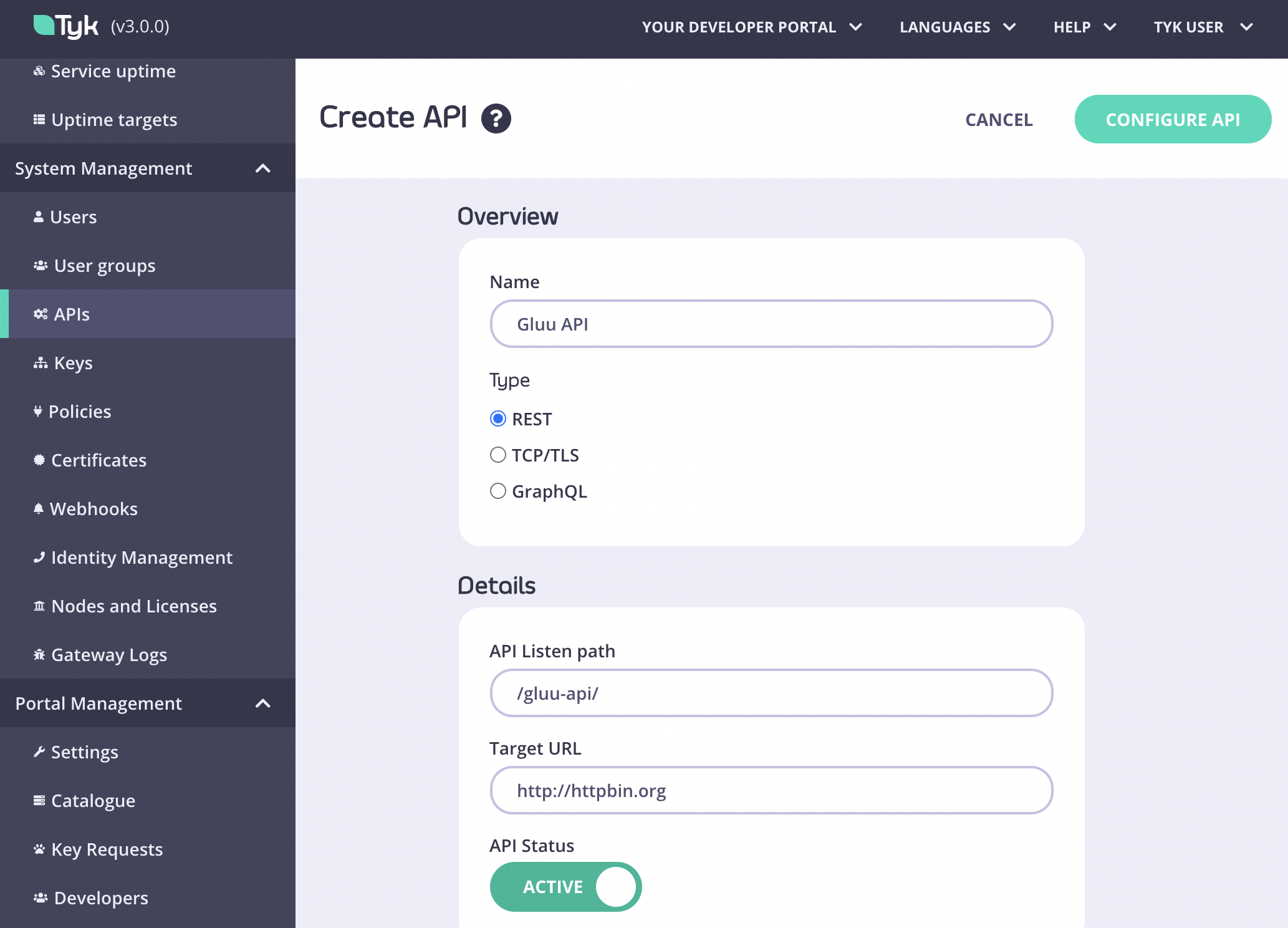
Setting up Tyk
Now you’re ready to set up Tyk. For compatibility reasons, check yourtyk_analytics.conf and make sure that a proper oauth_redirect_uri_separator parameter is set. You can use the following value:
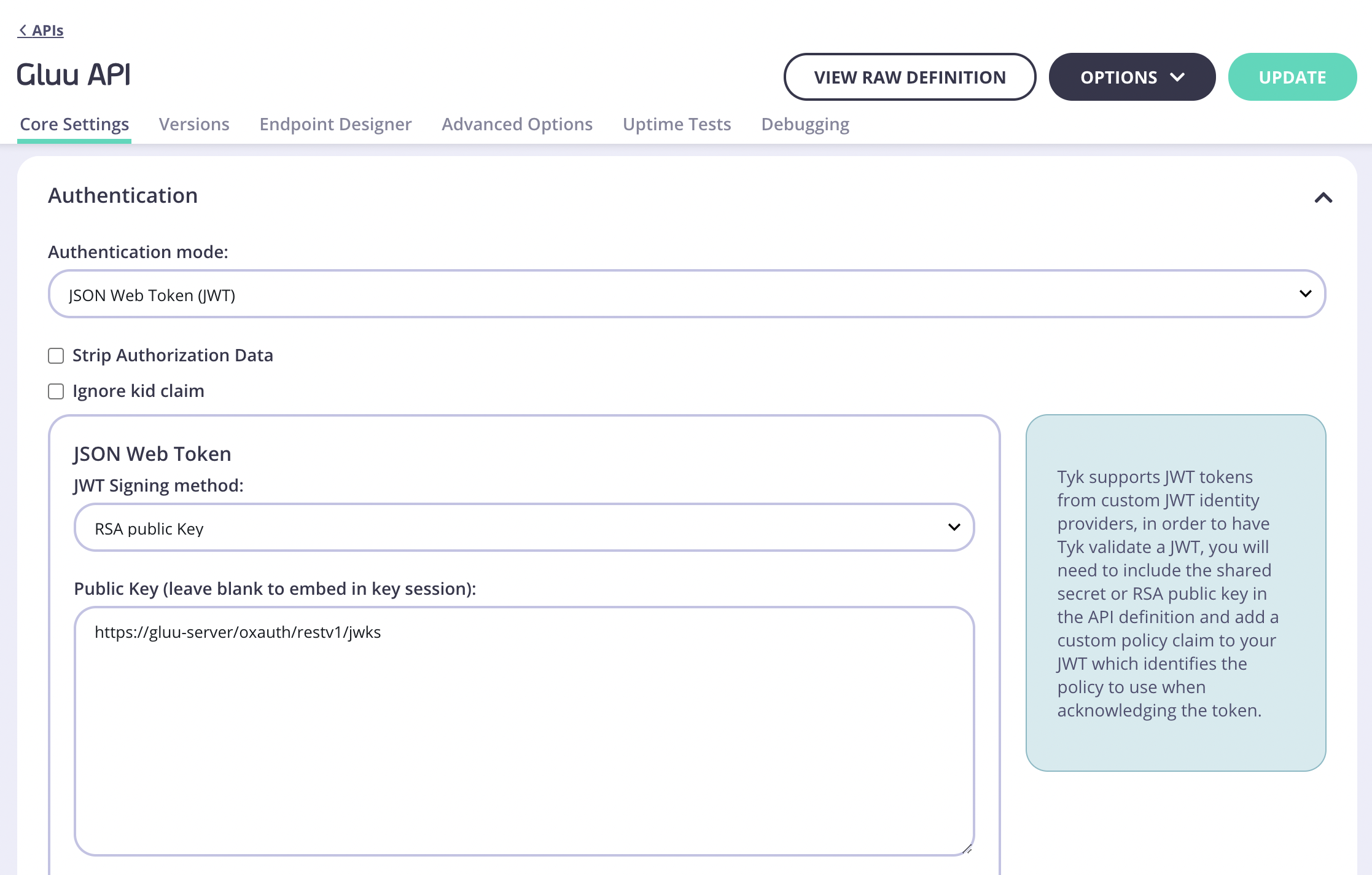
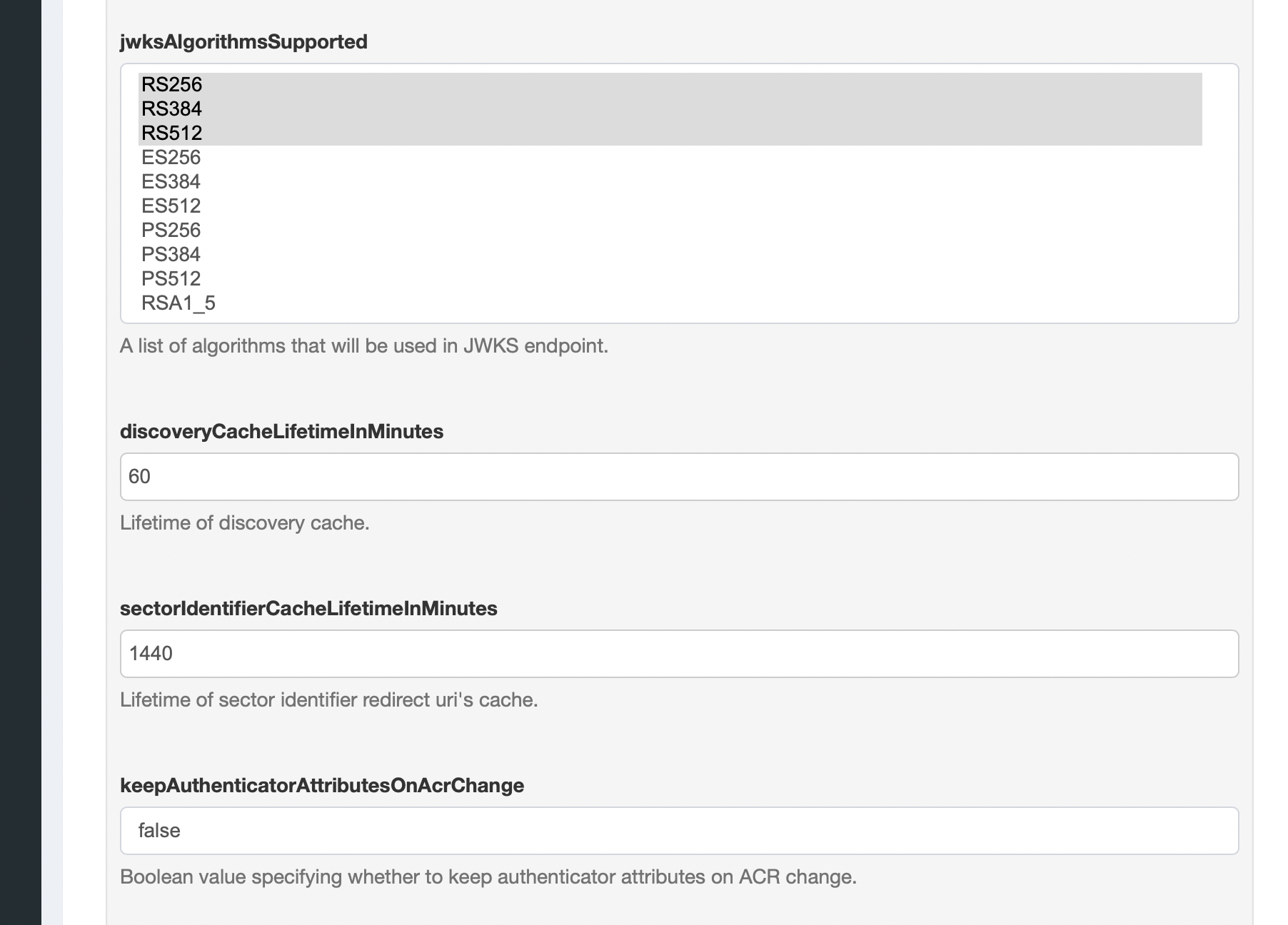
Where do I get the proper JWKS URI for my Gluu environment?The JWKS URI is a required field in the
.well-known/openid-configuration endpoint of your OpenID Connect Provider metadata. Typically found as "jwks_uri". Please see the spec https://openid.net/specs/openid-connect-discovery-1_0.html#ProviderConfigurationResponse for further information."client_id" and for Policy Field Name use "pol".
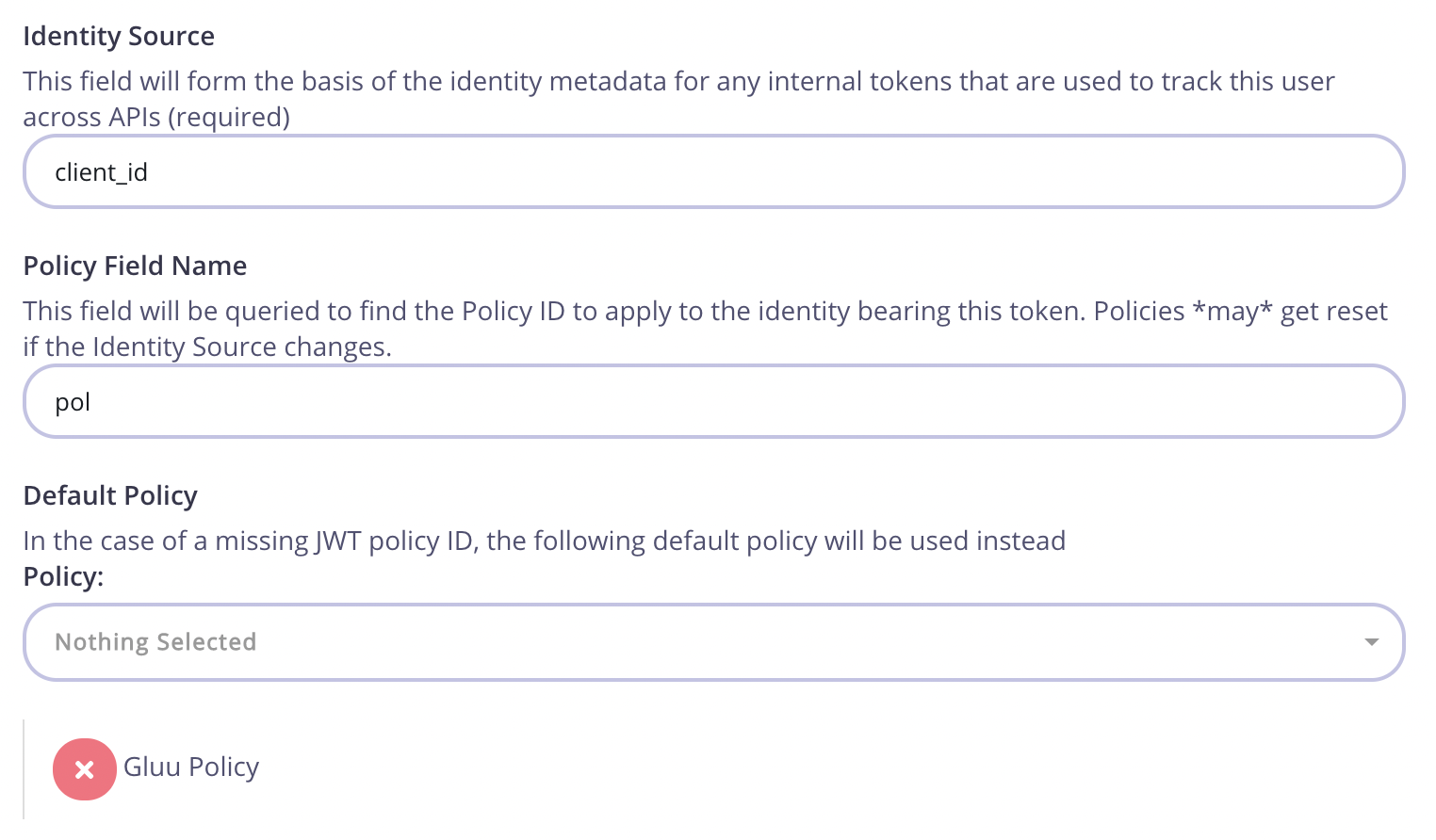
Click “Save” and switch to the “Policies” button under “System Management”. Once in this section, click on “Create a Policy” and call it “Gluu Policy”. Use the default values for this one. Remember to select the previously created “Gluu API” in the access rights section. You will also need to set an expiration setting for the keys.
After the policy is ready, switch back to the API settings and make sure that the API is using the appropriate policy:
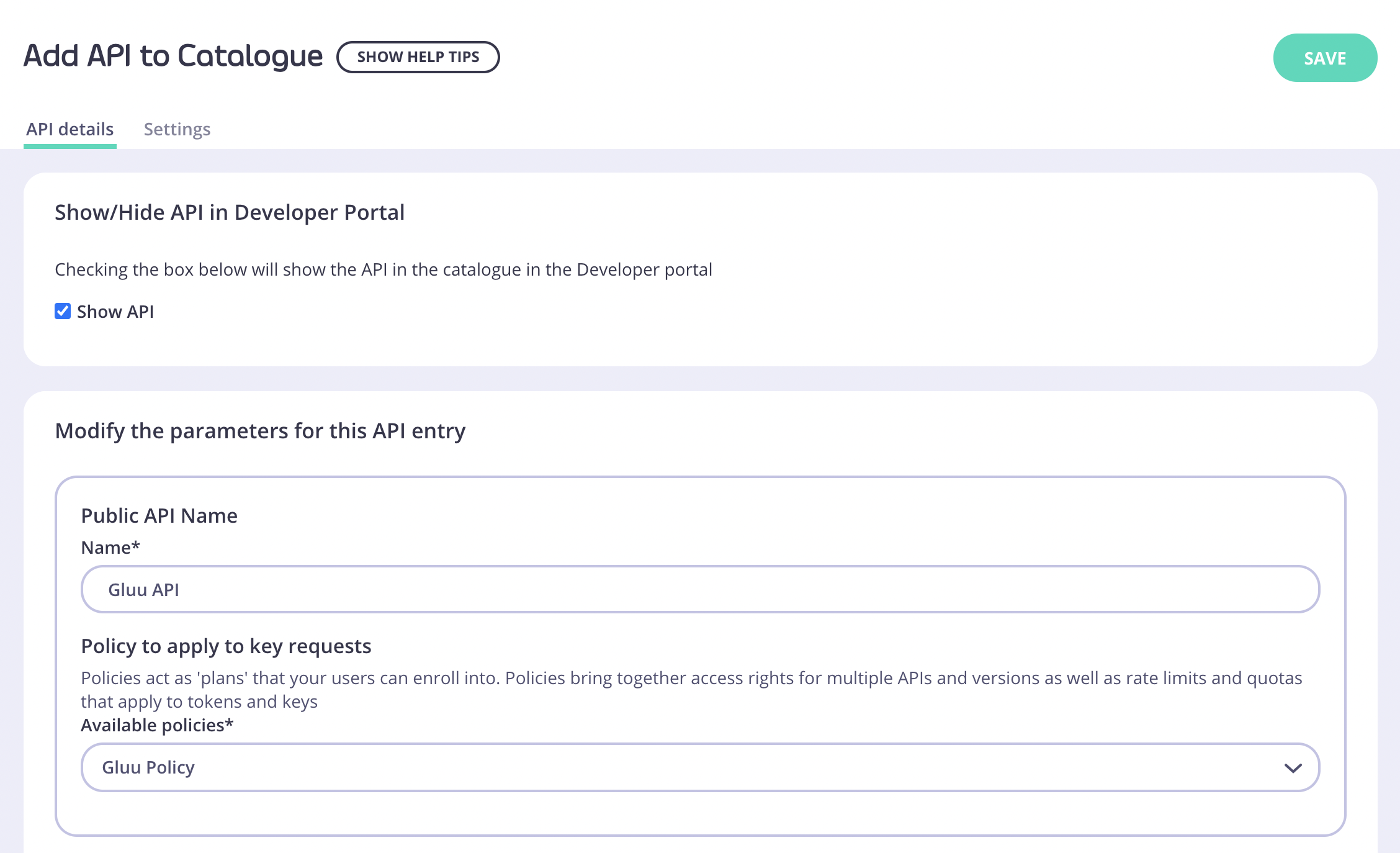
Tyk lets you set global portal settings that apply to all portal-listed APIs, in this guide we assume you’re enabling and setting up DCR for a single API. In case you want to enable DCR for all the APIs, you should go to the Settings section under Portal Management, and in the API Access tab you can enter your DCR settings there.
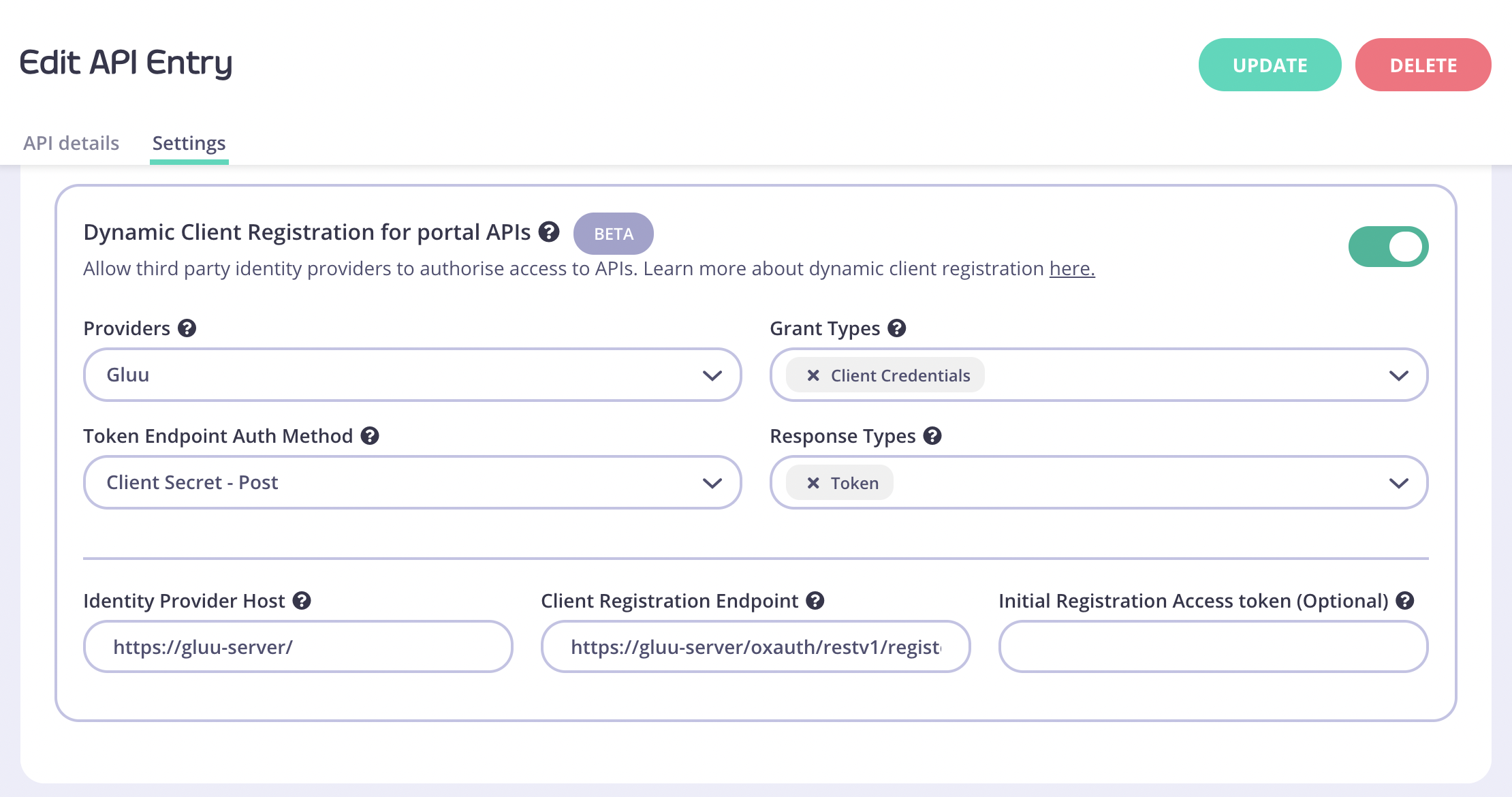
https://gluu-server/
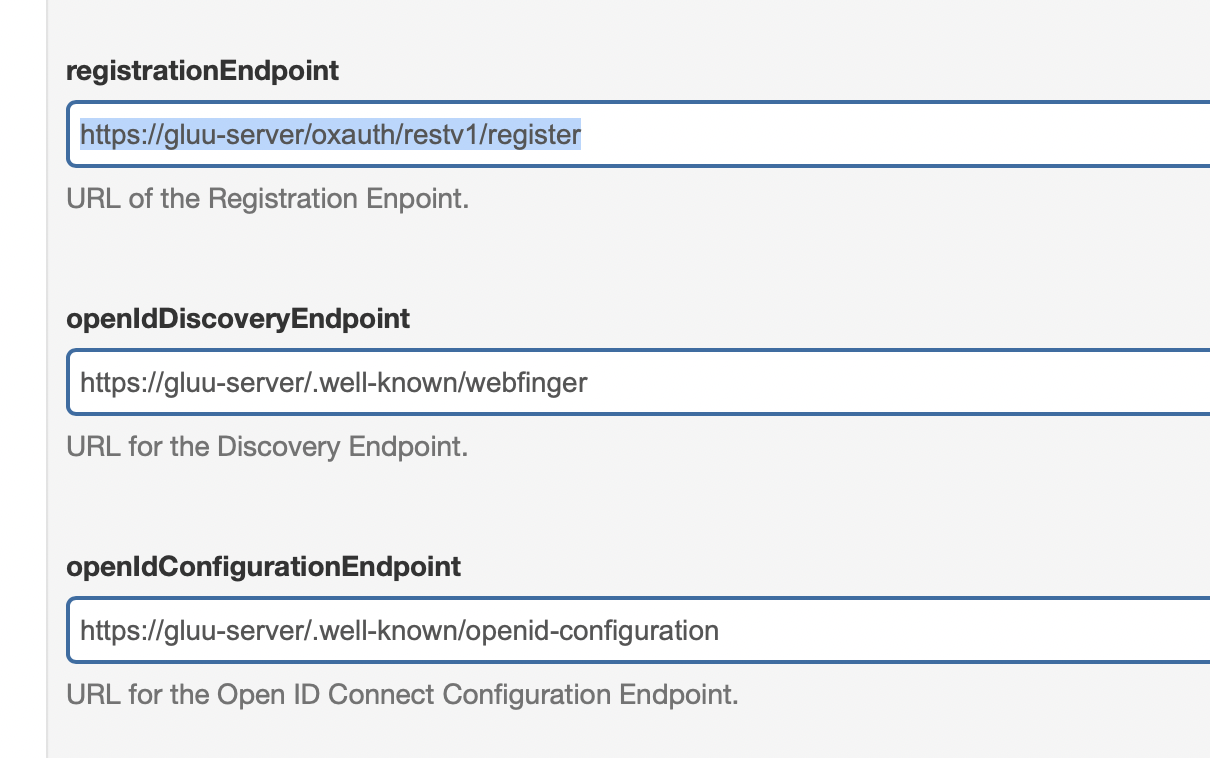
Client Registration Endpoint: OpenID Connect client registration endpoint. The value we use is https://gluu-server/oxauth/restv1/register
This value is found in your well-known discovery document as registration_endpoint. The well-known location URL is typically https://gluu-server/.well-known/openid-configuration (replace “gluu-server” with your hostname).
Initial Registration Access Token: the token that’s used to register new clients, this was generated in the early steps of the guide.
Testing the flow
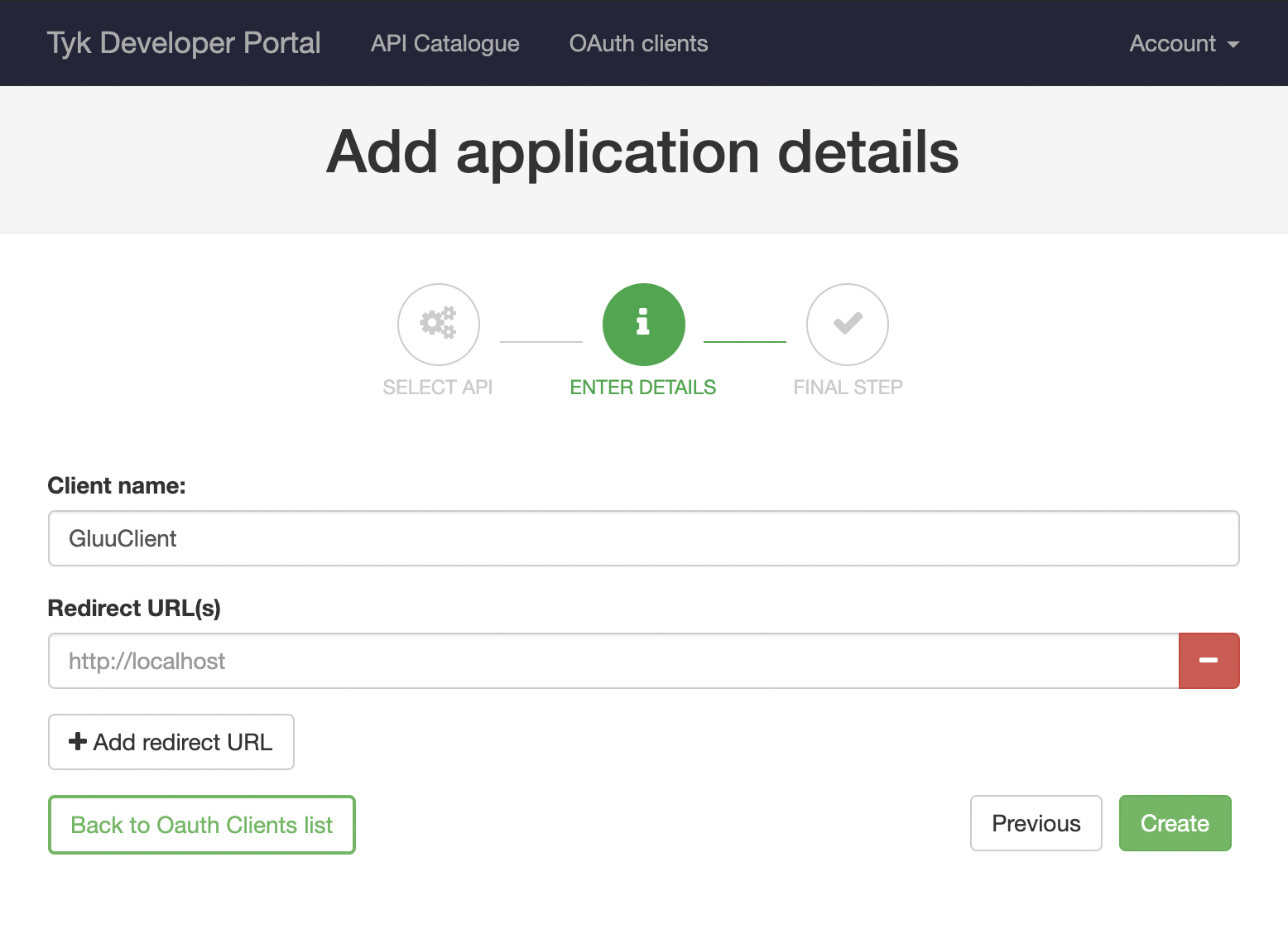
Now that both Tyk and Gluu are ready you can try the complete flow. Click “Developers” under “Portal Management”, then click “Add developer” and enter some basic information here to create a developer user. After the developer is created, open the portal, click on the “OAuth Clients” navigation bar button and follow the wizard: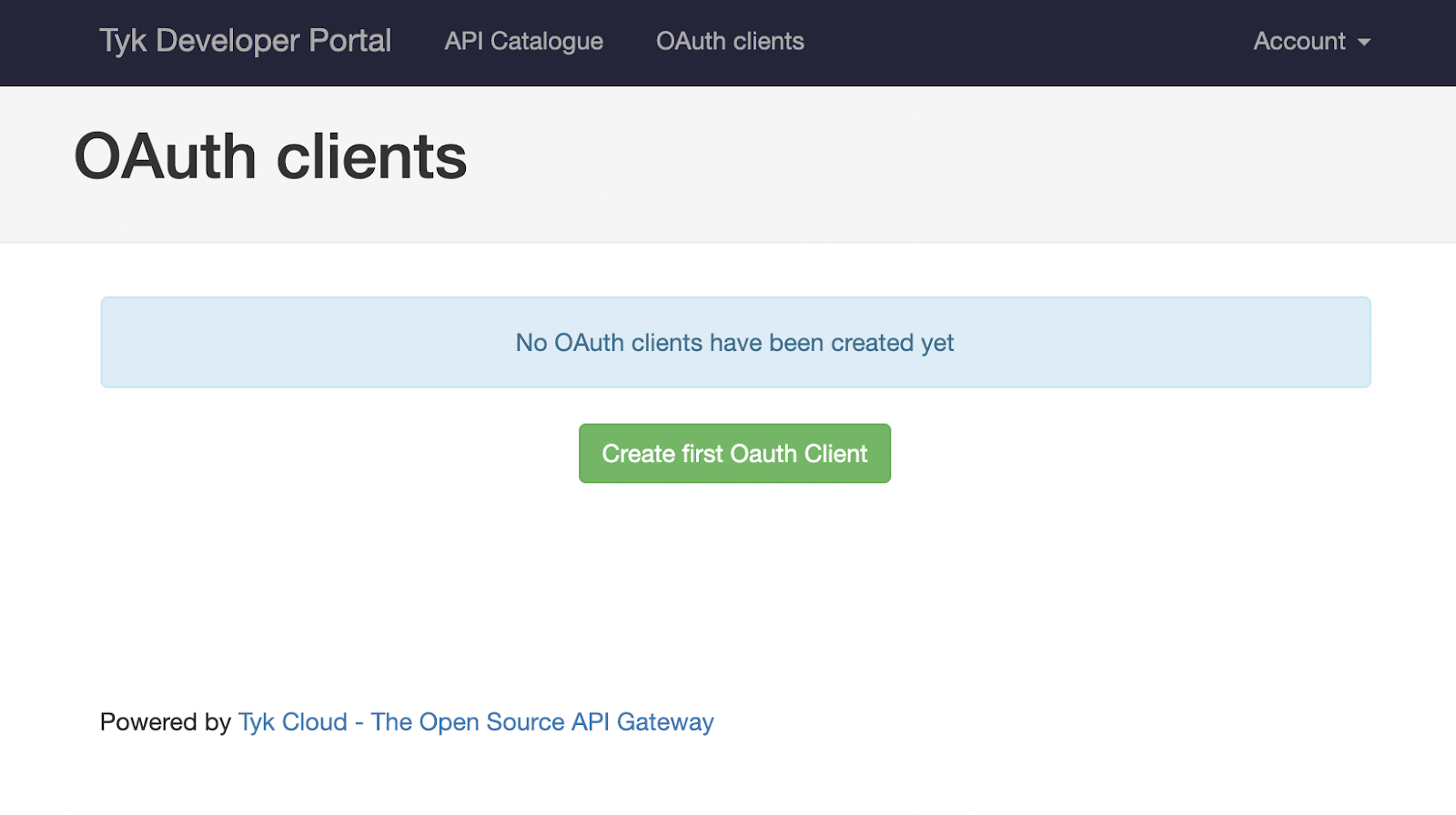
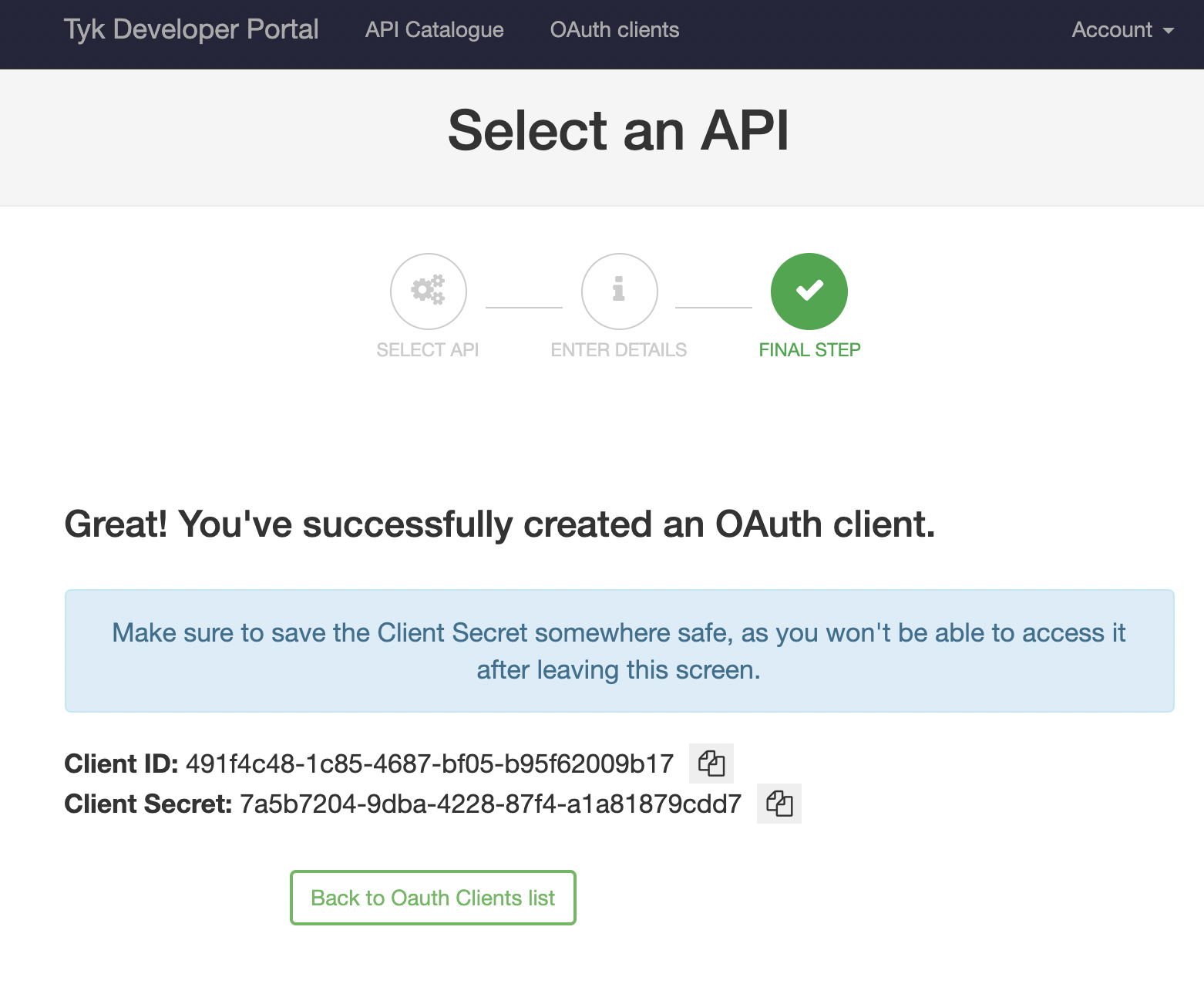
"token_endpoint".
For this example use the following: https://gluu-server/oxauth/restv1/token
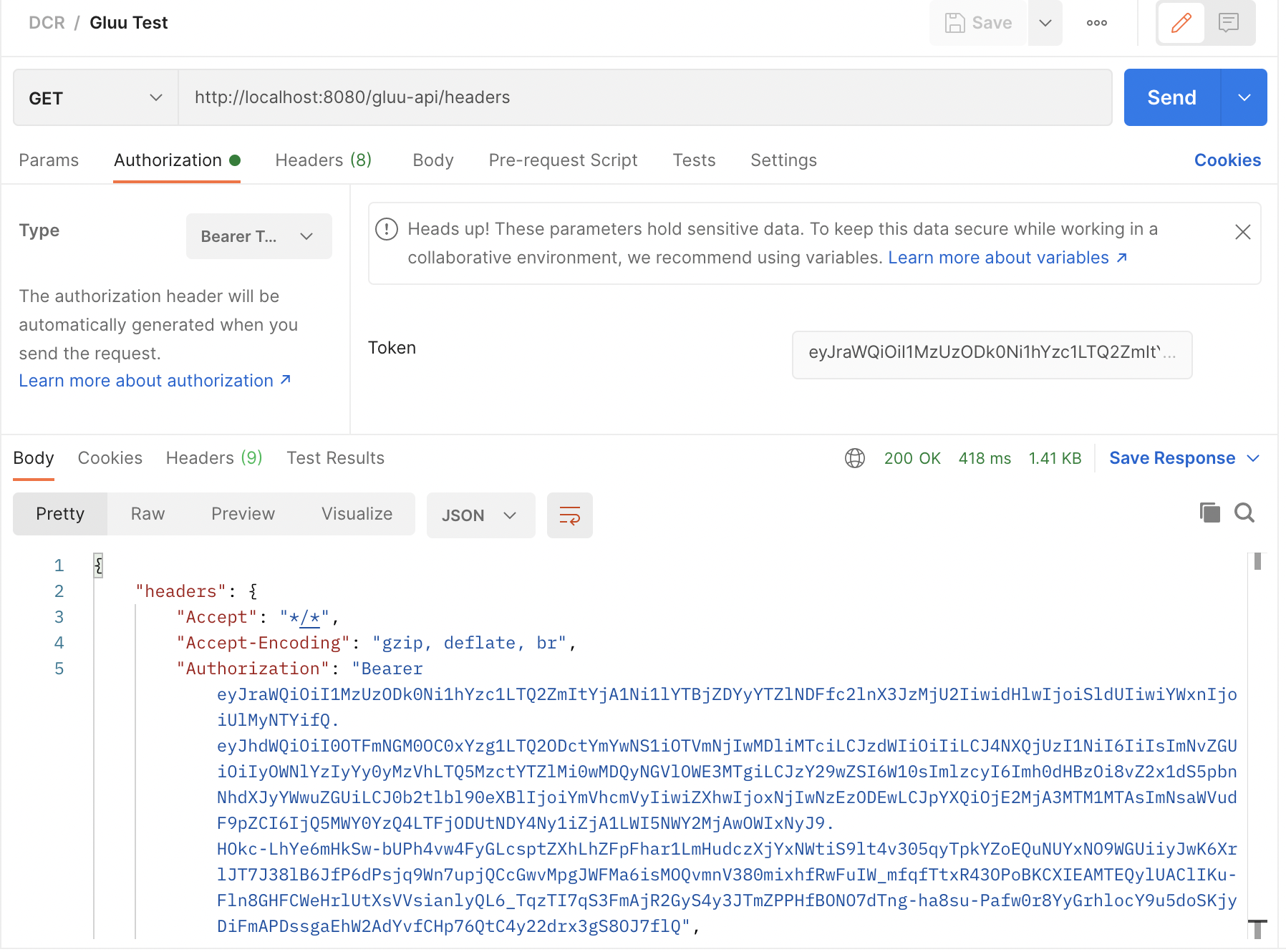
Your Postman request should contain the following body, where "client_id" and "client_secret" are the values you got from the developer portal:
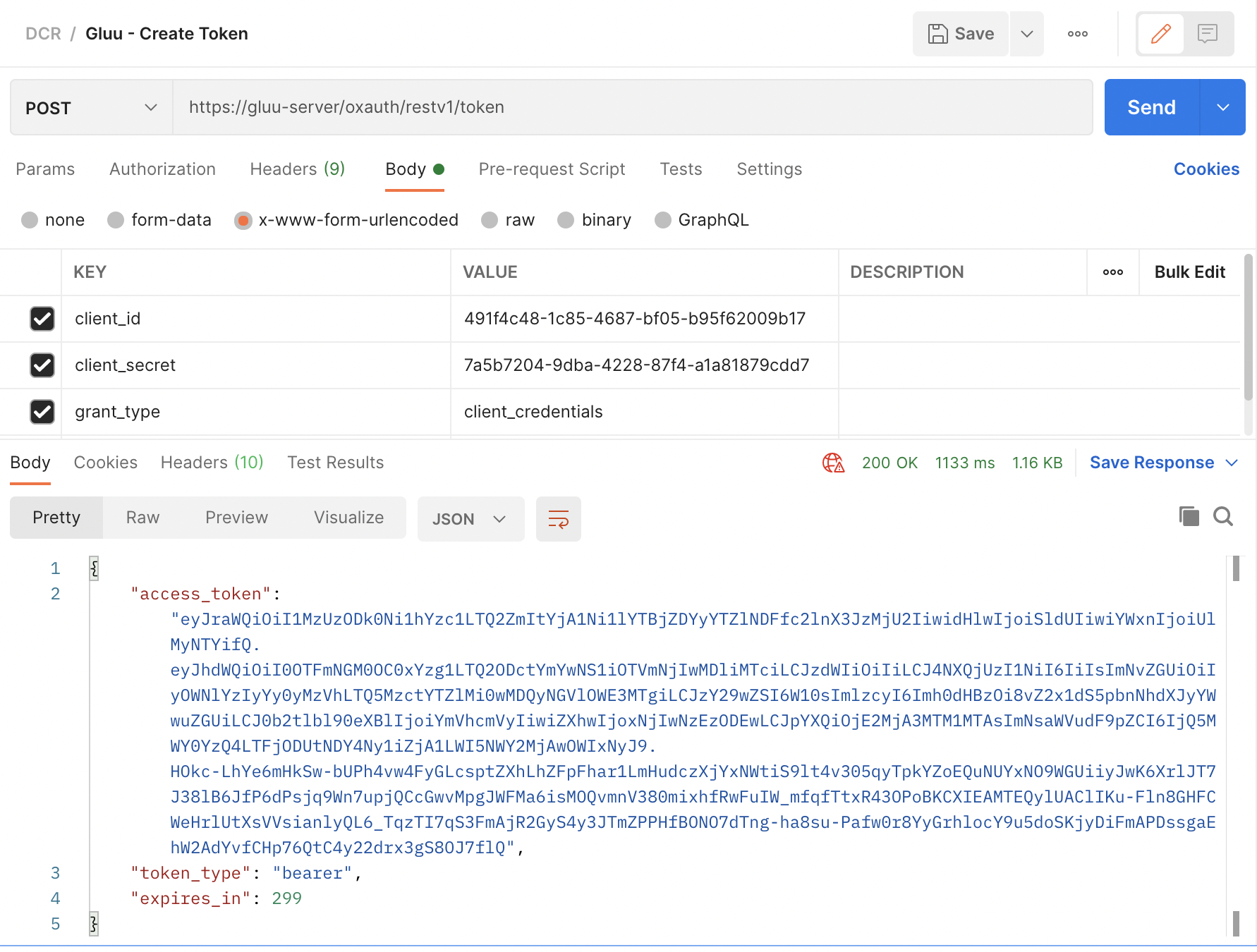
"access_token" and use it to access your “Gluu API”, this request will be proxied by Tyk: